Blog
The CrowdStrike Bug: Unraveling the Risk of Cascading Failures in Critical Systems

The recent CrowdStrike bug highlights the complex and sometimes fragile nature of our digital infrastructure, demonstrating how a simple software error can lead to cascading failures across critical systems worldwide. The bug originated from a malformed update in CrowdStrike’s Falcon platform—a widely used Endpoint Detection and Response (EDR) tool designed to protect against malware and cyber threats. Unlike typical applications, CrowdStrike’s EDR runs at the kernel level for deeper system monitoring, and this meant that when the update failed, it caused entire Windows operating systems to crash with the “Blue Screen of Death” (BSOD)(Home Page)(Enterprise Technology News and Analysis).
The faulty update affected millions of Windows machines globally, including those used by airlines, hospitals, and emergency services, severely disrupting critical infrastructure. The bug exploited memory access issues, causing the CrowdStrike software to reference invalid memory locations, ultimately leading to system crashes. The impact was so widespread because the update was automatically applied to a large number of systems overnight, leaving countless organizations with non-functional machines and no straightforward way to resolve the issue other than manual intervention, such as booting systems into “Safe Mode” to remove the update(Home Page)(Enterprise Technology News and Analysis).
The CrowdStrike incident serves as a wake-up call about the interconnectedness of modern software systems and the vulnerabilities inherent in automated updates. It wasn’t a malicious attack but instead a failure in the quality assurance process, illustrating how even top-tier cybersecurity tools can suffer from critical oversights. Security experts have pointed out the need for more rigorous quality assurance, especially for software that operates at such a fundamental level within operating systems. The bug also underscored the need for organizations to think about resilience, particularly in terms of planning for failures in key digital infrastructure components(Enterprise Technology News and Analysis)(Sonatype).
From a broader perspective, the incident reflects the risks associated with cyber-physical systems (CPS), such as those controlling infrastructure like oil pipelines or hospitals. These systems are often built with outdated technology that is difficult to upgrade, making them susceptible to disruptions like the CrowdStrike bug. With more than 25% of known vulnerabilities in critical infrastructure being tied to Windows systems, the incident further stresses the urgency of enhancing cyber defenses in these environments to avoid cascading failures that could cripple essential services(SiliconANGLE)(SiliconANGLE).
To mitigate such risks in the future, experts recommend several key actions:
- 1- Operationalizing Compensating Controls: Organizations should implement network segmentation and secure access controls to limit vulnerabilities.
- 2- Expanding Secure-by-Design Practices: Critical systems need to incorporate security at the design level, emphasizing secure manufacturing for medical and industrial devices.
- 3- Adopting Secure-by-Demand Programs: Organizations should evaluate the security practices of software vendors throughout the procurement process to ensure robust security measures are in place(SiliconANGLE)(SiliconANGLE).
The CrowdStrike bug is a stark reminder of the potential dangers lurking in the vast and interconnected digital ecosystems on which we rely. While bad updates are inevitable, their impacts do not have to be disastrous if proper planning and resilience measures are adopted. This incident serves as both a lesson and a catalyst for strengthening our digital defenses against not just accidental failures but also deliberate attacks.
Blog
Morocco Sets Sights on 70% 5G Coverage by 2030 With New License Launch
RABAT — July 26, 2025
In a landmark step toward digital transformation, Morocco’s National Telecommunications Regulatory Agency (ANRT) has officially launched the bidding process for 5G licenses, inviting national and international telecom operators to help deliver 25% population coverage by 2026 and 70% by 2030.
5G Strategy to Power FIFA World Cup and Beyond
The initiative aligns with Morocco’s preparations to co-host the 2030 FIFA World Cup and its broader Maroc Digital 2030 agenda. “This is about more than faster networks—it’s about our national future,” said Driss El Yazami, policy advisor at the Ministry of Digital Transition.
Highlights of the 5G Deployment Plan
- Initial rollouts in Casablanca, Rabat, Marrakech, and Tangier
- Smart infrastructure integration in stadiums and airports
- Spectrum allocation in 3.5GHz and mmWave bands
- Coverage expansion to underserved rural regions
From Urban Startups to Rural Farmers: 5G’s National Reach
5G is expected to revolutionize Moroccan society. Students will gain access to virtual classrooms, remote clinics will offer telemedicine, and farmers can deploy smart sensors. “Connectivity is empowerment,” said Amina El Mahdi, a tech entrepreneur in Fez.
Economic Impact and Cybersecurity Measures
The Ministry of Finance predicts 5G will boost GDP by 1.5% by 2030. All operators must meet strict cybersecurity, data localization, and interoperability standards monitored by ANRT and the National Cybersecurity Directorate.
2030 World Cup: Smart Stadiums and Global Broadcasts
With over 1.5 million visitors expected, 5G will support crowd management, mobile ticketing, HD broadcasts, and fan engagement zones across Moroccan host cities.
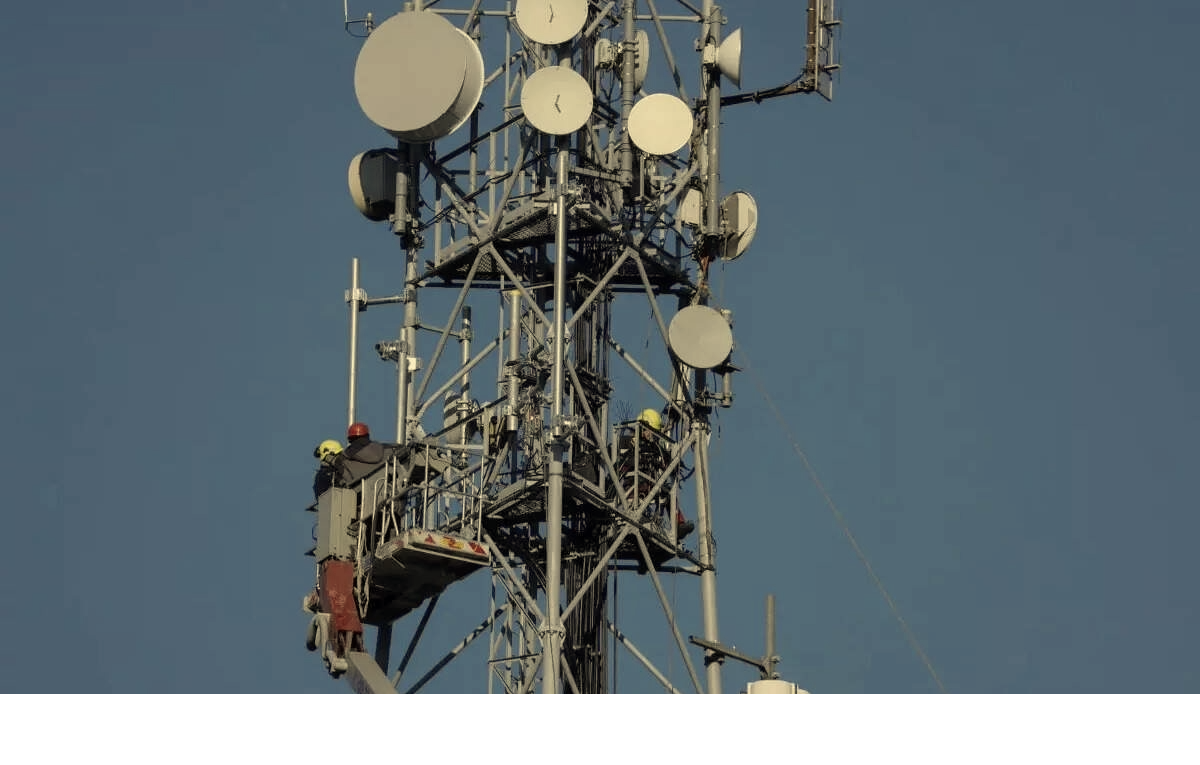
5G infrastructure being deployed in Morocco’s major cities ahead of FIFA 2030.
Blog
Critical Cyber Breach in Tunisia: Government Systems and Banks Hacked, Confidential Data for Sale

A coordinated cyberattack led by Moroccan hacker Jokeir 07x and groups Dark Hell 07x and Dr. Shell 08x compromises key Tunisian institutions, exposing government systems, banking infrastructure, and personal data to global exploitation.
Tunis, July 2025 — In an alarming escalation of cyber threats across North Africa, Tunisia has become the latest victim of a highly organized and devastating cyberattack. Orchestrated by Moroccan threat actor Jokeir 07x, in partnership with the groups Dark Hell 07x and Dr. Shell 08x, the operation has compromised critical national infrastructure—from government domains to private financial institutions.
“This is not just a defacement campaign—it’s full infrastructure penetration,” declared Jokeir 07x on Telegram.
The targets include the Ministry of Finance, Bank of Tunisia, BTK, and the Tunisian Academy of Banking and Finance, among others. The attackers claim full access to internal systems, including emails, financial records, developer platforms, and sensitive citizen data.
🏛️ Government Domain Breached: Ministry of Finance
The domain finances.gov.tn was infiltrated through 16 high-risk subdomains such as auth., gitlab.intra., mail., and login-tej. According to hacker statements, these allowed access to:
- Internal recruitment systems
- Budgetary information
- Developer repositories
- Administrative emails
This level of penetration indicates control over Tunisia’s digital authentication infrastructure and DevOps environment, raising severe concerns for national cybersecurity.
🏦 Banking Sector Compromised and Data Sold
Several banks were also impacted:
- Bank of Tunisia (bt.com.tn):
- Full customer database allegedly available for $4,000
- Individual bank accounts offered at $100
- 5-account bundles sold for $450
- BTK Bank (btknet.com) and Academy of Banking and Finance (abf.tn) also suffered complete breaches, including control over the sites and underlying systems.
The incident signals not just a data breach but the active commercialization of sensitive financial information on the dark web.
🔍 Technical Breakdown: How It Happened
Cybersecurity analysts have pointed to multiple failure points within Tunisia’s digital infrastructure:
- Web Application Vulnerabilities:
- SQL Injection
- File Upload flaws
- XSS
- Remote File Inclusion (RFI)
- SSO and Mail System Exploitation:
- Session hijacking likely
- Weak session/cookie management
- GitLab Exposure:
- Unauthorized access to internal GitLab revealed API tokens, credentials, and system architecture
- Lack of Security Infrastructure:
- No evidence of WAF, IDS, or SIEM defense
- No active monitoring or response systems
- Inadequate Data Protection:
- Absence of encryption, data masking, or tokenization
- Entire banking datasets available in plain text
⚠️ The Fallout: Trust, Security, and Reputation
This attack lays bare the vulnerabilities in Tunisia’s cyber defenses, damaging public trust in both government institutions and the banking sector. The country’s financial and administrative data has now surfaced on international black markets, with potential long-term repercussions for national security and economic stability.
💡 Urgent Recommendations for Recovery and Reform
Cybersecurity professionals are urging Tunisia to immediately:
- Establish internal SOC (Security Operations Centers)
- Mandate routine penetration testing
- Enforce multi-factor authentication (MFA)
- Implement end-to-end data encryption
- Audit and secure GitLab instances
- Conduct staff training on social engineering threats
- Deploy real-time code and data monitoring
“Being hacked is not the shame—failing to learn from it is,” noted a Tunisian cybersecurity analyst. “The future belongs to those who invest in digital resilience, not legacy infrastructure.”
Blog
Cloud Wars 2025: Full Breakdown of Azure, AWS, and Google Cloud Services You Need to Know
As cloud computing reshapes digital infrastructure, this side-by-side comparison of services across Microsoft Azure, Amazon Web Services (AWS), and Google Cloud Platform (GCP) empowers IT professionals and organizations to make informed decisions.
Cloud Wars: Breaking Down the Giants
In today’s digital-first world, cloud computing isn’t just a trend—it’s the backbone of enterprise IT. Whether you’re a startup deploying an app or a global corporation migrating legacy systems, choosing the right cloud provider can make or break your operations. A newly circulated Cloud Services Comparison Cheatsheet provides an invaluable visual breakdown of offerings from Microsoft Azure, Amazon Web Services (AWS), and Google Cloud Platform (GCP), the three dominant players in the cloud arena.
Technical Deep Dive: Key Service Categories Compared
This infographic categorizes over 25 essential cloud services and maps each across Azure, AWS, and GCP equivalents. Here’s what stands out:
1. Compute Services
- Azure: Virtual Machines
- AWS: EC2 (Elastic Compute Cloud)
- Google Cloud: Compute Engine
These services provide scalable virtual server environments, with options for predefined or custom machine types. Azure and AWS offer more mature ecosystems with hybrid cloud integrations, while GCP emphasizes fast boot times and sustained-use discounts.
2. Object Storage
- Azure Blob Storage
- Amazon S3
- Google Cloud Storage
All three services allow you to store large amounts of unstructured data. AWS S3 is known for its advanced features (like S3 Glacier), while Azure Blob integrates well with Microsoft services, and GCP offers multi-regional redundancy by default.
3. Serverless Computing
- Azure Functions
- AWS Lambda
- Google Cloud Functions
Serverless solutions allow developers to execute code without managing servers. AWS Lambda leads in ecosystem maturity, while Azure and Google offer solid integrations with their respective developer tools.
4. Content Delivery Networks (CDNs)
- Azure CDN, AWS CloudFront, and Google Cloud CDN
All three platforms offer global distribution of content to reduce latency. AWS CloudFront is widely adopted in large-scale enterprise environments, while Google leverages its backbone network to deliver high-speed content.
Security & Identity Management
Cloud security remains a priority as data breaches and compliance requirements escalate.
- Identity and Access Management (IAM) is offered across platforms with Azure Active Directory, AWS IAM, and Google Cloud IAM.
- Key Management Services (KMS) ensure secure handling of encryption keys across all three.
- Compliance tools like Azure Trust Center, AWS Cloud HSM, and Google Cloud Security help enterprises adhere to global regulations like GDPR, HIPAA, and ISO/IEC.
Specialized Services: AI, Containers, and Analytics
- Analytics: Azure Stream Analytics, Amazon Kinesis, and Google Dataflow enable real-time data processing.
- Containers: Azure Kubernetes Service (AKS), Amazon EKS, and Google Kubernetes Engine (GKE) support modern container orchestration.
- Automation: Each provider supports automation—Azure with Azure Automation, AWS with OpsWorks, and GCP with Deployment Manager.
Notable Differences
Some categories reveal gaps:
- Google Cloud lacks direct equivalents for services like DNS management (Route 53, Azure DNS) or cloud notifications (AWS SNS, Azure Notification Hub).
- Azure leads in hybrid cloud features due to its integration with Windows Server and on-prem tools.
- AWS offers the broadest service portfolio, making it ideal for complex multi-cloud or global enterprise setups.







