data breaches
Activision Pulls Call of Duty: WWII from Microsoft Store After Players Hacked

Activision has been forced to take down the Microsoft Store version of Call of Duty: WWII after players began reporting serious cybersecurity incidents tied to the game’s PC build. The 2017 title, recently relaunched on Game Pass, was exploited by malicious actors who used a previously undisclosed flaw to gain remote access to players’ machines, leading to a rare but impactful shutdown of a major online game.
The takedown highlights growing concerns in the gaming industry about client-side vulnerabilities, supply chain risks, and the consequences of understaffed cybersecurity teams at major studios.
Activision’s Statement and Action
While Activision has not released detailed technical findings, the company confirmed in a brief announcement that it had “temporarily disabled access to the Microsoft Store build of Call of Duty: WWII to investigate a security vulnerability impacting some players on PC.”
The vulnerability reportedly allowed attackers to use compromised lobbies or peer-to-peer game traffic to deliver malicious payloads, potentially leveraging code injection or DLL sideloading techniques commonly seen in game hacking and modding communities.
Technical Breakdown: Possible Exploit Vectors
Based on independent research and prior case patterns in multiplayer gaming environments, several likely vectors are being investigated by the cybersecurity community:
1. Remote Code Execution via Modded Lobbies
Mechanism: Attackers may have hosted or injected into custom game lobbies where malicious scripts or modified game logic could be pushed to connected clients.
Risk: Once a player joined, arbitrary code could be executed locally under the same privileges as the game process.
2. DLL Injection via Game Mod Loaders
Mechanism: The PC version may have lacked proper signature verification or binary integrity checks, allowing attackers to inject custom DLLs that executed upon game launch.
Risk: These DLLs could serve as backdoors or dropper payloads for larger malware frameworks.
3. Peer-to-Peer (P2P) Packet Exploits
Mechanism: Older versions of CoD games use P2P networking for multiplayer. An attacker could send crafted UDP packets that triggered buffer overflows or memory corruption in the game’s network handling code.
Risk: Exploits could hijack client memory, allowing attackers to execute code or crash systems remotely.
4. Supply Chain Misconfiguration
Mechanism: The version distributed via Microsoft Store/Game Pass might have had unpatched legacy libraries or a misconfigured update pipeline.
Risk: Attackers could abuse overlooked dependencies (e.g., outdated DirectX components or input libraries) to trigger local privilege escalation or code execution.
Impact and Industry Fallout
The issue is particularly sensitive given that the title was newly added to Microsoft Game Pass, putting it in front of thousands of unsuspecting players—many of whom may not have enabled robust endpoint protections.
“This is a textbook example of why legacy titles need just as much security investment as live-service games,” said a former developer on Activision’s anti-cheat team.
Activision’s Security History and Response
The incident comes at a time when Activision has faced multiple rounds of layoffs, some of which impacted its cybersecurity and anti-cheat divisions. Industry insiders report that several experienced infosec engineers were cut in early 2024 as part of cost-reduction efforts.
By contrast, other publishers such as Riot Games, Ubisoft, and Epic Games have ramped up internal cybersecurity hiring, threat modeling, and real-time telemetry systems in response to a rise in targeted game-based exploits.
What Happens Next?
- The Microsoft Store version of CoD: WWII remains offline pending investigation.
- No confirmation yet if players will receive security patches or credit for downtime.
- Activision is expected to publish a CVE bulletin or threat advisory if the issue involves system-level risk.
Key Lessons for the Gaming Industry
- Legacy code must be actively audited before being redistributed.
- Peer-to-peer multiplayer networking is inherently risky in 2025.
- Layoffs affecting security staff can have long-term operational consequences.
If confirmed, this will be one of the few known instances where a triple-A video game has been delisted due to real-world cyberattacks on its player base.
data breaches
Cloudflare Outage Disrupts Global Internet — Company Restores Services After Major Traffic Spike

November 18, 2025 — MAG212NEWS
A significant outage at Cloudflare, one of the world’s leading internet infrastructure providers, caused widespread disruptions across major websites and online services on Tuesday. The incident, which began mid-morning GMT, temporarily affected access to platforms including ChatGPT, X (formerly Twitter), and numerous business, government, and educational services that rely on Cloudflare’s network.
According to Cloudflare, the outage was triggered by a sudden spike in “unusual traffic” flowing into one of its core services. The surge caused internal components to return 500-series error messages, leaving users unable to access services across regions in Europe, the Middle East, Asia, and North America.
Impact Across the Web
Because Cloudflare provides DNS, CDN, DDoS mitigation, and security services for millions of domains — powering an estimated 20% of global web traffic — the outage had swift and wide-reaching effects.
Users reported:
- Website loading failures
- “Internal Server Error” and “Bad Gateway” messages
- Slowdowns on major social platforms
- Inaccessibility of online tools, APIs, and third-party authentication services
The outage also briefly disrupted Cloudflare’s own customer-support portal, highlighting the interconnected nature of the company’s service ecosystem.
Cloudflare’s Response and Restoration
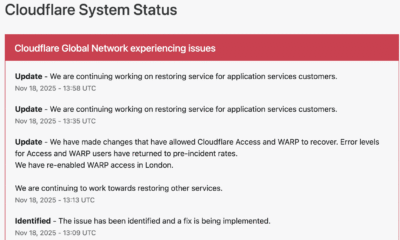
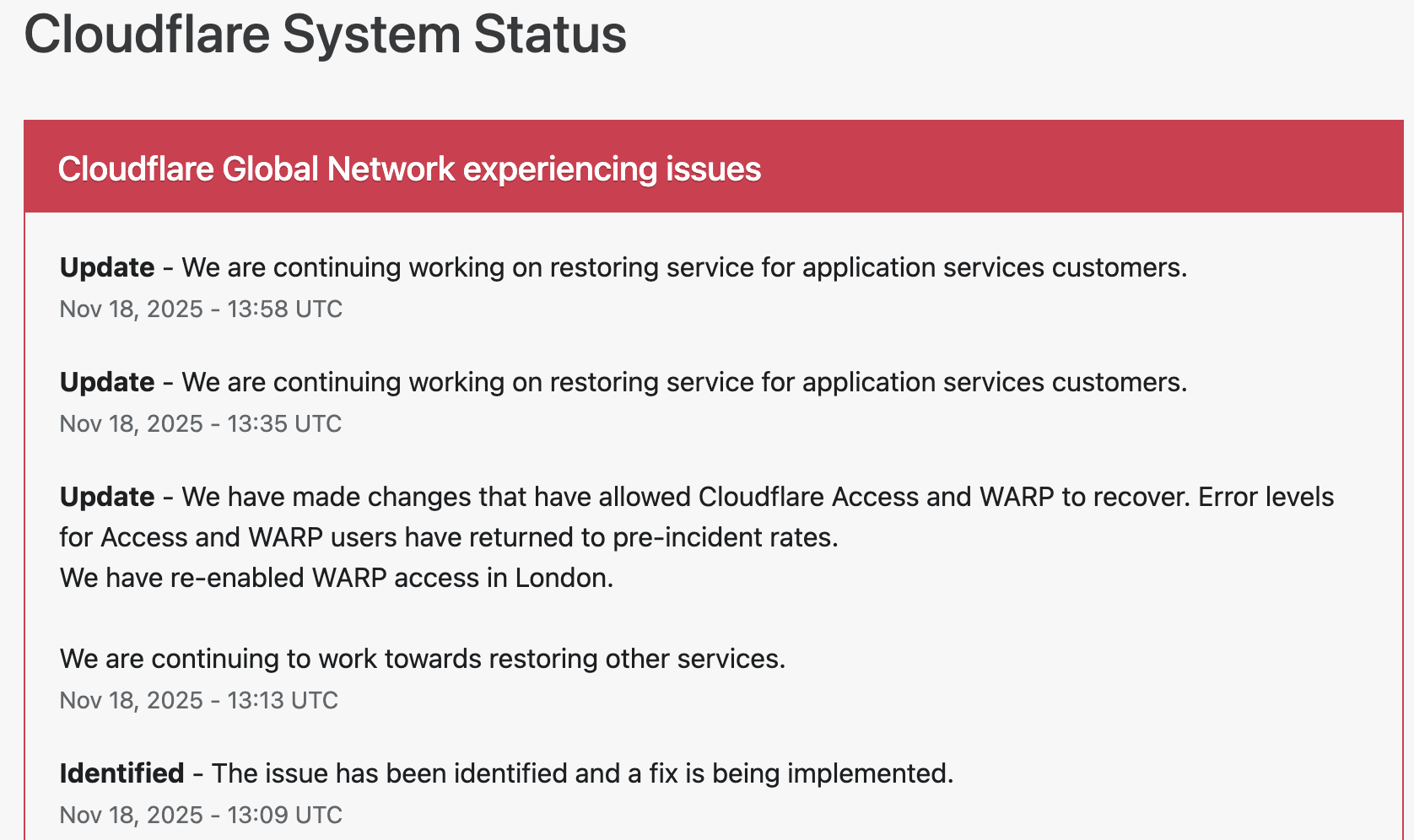
Cloudflare responded within minutes, publishing updates on its official status page and confirming that engineering teams were investigating the anomaly.
The company took the following steps to restore operations:
1. Rapid Detection and Acknowledgement
Cloudflare engineers identified elevated error rates tied to an internal service degradation. Public communications were issued to confirm the outage and reassure customers.
2. Isolating the Affected Systems
To contain the disruption, Cloudflare temporarily disabled or modified specific services in impacted regions. Notably, the company deactivated its WARP secure-connection service for users in London to stabilize network behavior while the fix was deployed.
3. Implementing Targeted Fixes
Technical teams rolled out configuration changes to Cloudflare Access and WARP, which successfully reduced error rates and restored normal traffic flow. Services were gradually re-enabled once systems were verified stable.
4. Ongoing Root-Cause Investigation
While the unusual-traffic spike remains the confirmed trigger, Cloudflare stated that a full internal analysis is underway to determine the exact source and prevent a recurrence.
By early afternoon UTC, Cloudflare confirmed that systems had returned to pre-incident performance levels, and affected services worldwide began functioning normally.
Why This Matters
Tuesday’s outage underscores a critical truth about modern internet architecture: a handful of infrastructure companies underpin a massive portion of global online activity. When one of them experiences instability — even briefly — the ripple effects are immediate and worldwide.
For businesses, schools, governments, and content creators, the incident is a reminder of the importance of:
- Redundant DNS/CDN providers
- Disaster-recovery and failover plans
- Clear communication protocols during service outages
- Vendor-dependency risk assessments
Cloudflare emphasized that no evidence currently points to a cyberattack, though the nature of the traffic spike remains under investigation.
Looking Ahead
As Cloudflare completes its post-incident review, the company is expected to provide a detailed breakdown of the technical root cause and outline steps to harden its infrastructure. Given Cloudflare’s central role in global internet stability, analysts say the findings will be watched closely by governments, cybersecurity professionals, and enterprise clients.
For now, services are restored — but the outage serves as a powerful reminder of how interconnected and vulnerable the global web can be.
data breaches
Cloudflare Outage Analysis: Systemic Failure in Edge Challenge Mechanism Halts Global Traffic
SAN FRANCISCO, CA — A widespread disruption across major internet services, including AI platform ChatGPT and social media giant X (formerly Twitter), has drawn critical attention to the stability of core internet infrastructure. The cause traces back to a major service degradation at Cloudflare, the dominant content delivery network (CDN) and DDoS mitigation provider. Users attempting to access affected sites were met with an opaque, yet telling, error message: “Please unblock challenges.cloudflare.com to proceed.”
This incident was not a simple server crash but a systemic failure within the crucial Web Application Firewall (WAF) and bot management pipeline, resulting in a cascade of HTTP 5xx errors that effectively severed client-server connections for legitimate users.
The Mechanism of Failure: challenges.cloudflare.com
The error message observed globally points directly to a malfunction in Cloudflare’s automated challenge system. The subdomain challenges.cloudflare.com is central to the company’s security and bot defense strategy, acting as an intermediate validation step for traffic suspected of being malicious (bots, scrapers, or DDoS attacks).
This validation typically involves:
- Browser Integrity Check (BIC): A non-invasive test ensuring the client browser is legitimate.
- Managed Challenge: A dynamic, non-interactive proof-of-work check.
- Interactive Challenge (CAPTCHA): A final, user-facing verification mechanism.
In a healthy system, a user passing through Cloudflare’s edge network is either immediately granted access or temporarily routed to this challenge page for verification.
During the outage, however, the Challenge Logic itself appears to have failed at the edge of Cloudflare’s network. When the system was invoked (likely due to high load or a misconfiguration), the expected security response—a functional challenge page—returned an internal server error (a 500-level status code). This meant:
- The Request Loop: Legitimate traffic was correctly flagged for a challenge, but the server hosting the challenge mechanism failed to process or render the page correctly.
- The
HTTP 500Cascade: Instead of displaying the challenge, the Cloudflare edge server returned a “500 Internal Server Error” to the client, sometimes obfuscated by the text prompt to “unblock” the challenges domain. This effectively created a dead end, blocking authenticated users from proceeding to the origin server (e.g., OpenAI’s backend for ChatGPT).
Technical Impact on Global Services
The fallout underscored the concentration risk inherent in modern web architecture. As a reverse proxy, Cloudflare sits between the end-user and the origin server for a vast percentage of the internet.
For services like ChatGPT, which rely heavily on fast, secure, and authenticated API calls and constant data exchange, the WAF failure introduced severe latency and outright connection refusal. A failure in Cloudflare’s global network meant that fundamental features such as DNS resolution, TLS termination, and request routing were compromised, leading to:
- API Timeouts: Applications utilizing Cloudflare’s API for configuration or deployment experienced critical failures.
- Widespread Service Degradation: The systemic 5xx errors at the L7 (Application Layer) caused services to appear “down,” even if the underlying compute resources and databases of the origin servers remained fully operational.
Cloudflare’s official status updates confirmed they were investigating an issue impacting “multiple customers: Widespread 500 errors, Cloudflare Dashboard and API also failing.” While the exact trigger was later traced to an internal platform issue (in some historical Cloudflare incidents, this has been a BGP routing error or a misconfigured firewall rule pushed globally), the user-facing symptom highlighted the fragility of relying on a single third-party for security and content delivery on a global scale.
Mitigation and the Single Point of Failure
While Cloudflare teams worked to roll back configuration changes and isolate the fault domain, the incident renews discussion on the “single point of failure” doctrine. When a critical intermediary layer—responsible for security, routing, and caching—experiences a core logic failure, the entire digital economy resting on it is exposed.
Engineers and site reliability teams are now expected to further scrutinize multi-CDN and multi-cloud strategies, ensuring that critical application traffic paths are not entirely dependent on a single third-party’s edge infrastructure, a practice often challenging due to cost and operational complexity. The “unblock challenges” error serves as a stark reminder of the technical chasm between a user’s browser and the complex, interconnected security apparatus that underpins the modern web.
data breaches
Manufacturing Software at Risk from CVE-2025-5086 Exploit
Dassault Systèmes patches severe vulnerability in Apriso manufacturing software that could let attackers bypass authentication and compromise factories worldwide.
A newly disclosed flaw, tracked as CVE-2025-5086, poses a major security risk to manufacturers using Dassault Systèmes’ DELMIA Apriso platform. The bug could allow unauthenticated attackers to seize control of production environments, prompting urgent patching from the vendor and warnings from cybersecurity experts.
A critical vulnerability in DELMIA Apriso, a manufacturing execution system used by global industries, could let hackers bypass authentication and gain full access to sensitive production data, according to a security advisory published this week.
Dassault Systèmes confirmed the flaw, designated CVE-2025-5086, affects multiple versions of Apriso and scored 9.8 on the CVSS scale, placing it in the “critical” category. Researchers said the issue stems from improper authentication handling that allows remote attackers to execute privileged actions without valid credentials.
The company has released security updates and urged immediate deployment, warning that unpatched systems could become prime targets for industrial espionage or sabotage. The flaw is particularly alarming because Apriso integrates with enterprise resource planning (ERP), supply chain, and industrial control systems, giving attackers a potential foothold in critical infrastructure.
- “This is the kind of vulnerability that keeps CISOs awake at night,” said Maria Lopez, industrial cybersecurity analyst at Kaspersky ICS CERT. “If exploited, it could shut down production lines or manipulate output, creating enormous financial and safety risks.”
- “Manufacturing software has historically lagged behind IT security practices, making these flaws highly attractive to threat actors,” noted James Patel, senior researcher at SANS Institute.
- El Mostafa Ouchen, cybersecurity author, told MAG212News: “This case shows why manufacturing execution systems must adopt zero-trust principles. Attackers know that compromising production software can ripple across supply chains and economies.”
- “We are actively working with customers and partners to ensure systems are secured,” Dassault Systèmes said in a statement. “Patches and mitigations have been released, and we strongly recommend immediate updates.”
Technical Analysis
The flaw resides in Apriso’s authentication module. Improper input validation in login requests allows attackers to bypass session verification, enabling arbitrary code execution with administrative privileges. Successful exploitation could:
- Access or modify production databases.
- Inject malicious instructions into factory automation workflows.
- Escalate attacks into connected ERP and PLM systems.
Mitigations include applying vendor patches, segmenting Apriso servers from external networks, enforcing MFA on supporting infrastructure, and monitoring for abnormal authentication attempts.
Impact & Response
Organizations in automotive, aerospace, and logistics sectors are particularly exposed. Exploited at scale, the vulnerability could cause production delays, supply chain disruptions, and theft of intellectual property. Security teams are advised to scan their environments, apply updates, and coordinate incident response planning.
Background
This disclosure follows a string of high-severity flaws in industrial and operational technology (OT) software, including vulnerabilities in Siemens’ TIA Portal and Rockwell Automation controllers. Experts warn that adversaries—ranging from ransomware gangs to state-sponsored groups—are increasingly focusing on OT targets due to their high-value disruption potential.
Conclusion
The CVE-2025-5086 flaw underscores the urgency for manufacturers to prioritize cybersecurity in factory software. As digital transformation accelerates, securing industrial platforms like Apriso will be critical to ensuring business continuity and protecting global supply chains.