International
GPT-5 Is Here – The Dawn of a New AI Era Begins

OpenAI’s GPT-5 launch marks a turning point in artificial intelligence, promising unprecedented power and igniting fierce competition in the AI industry.
GPT-5’s Game-Changing Debut
“We are introducing GPT-5, our best AI system yet… a significant leap in intelligence over all our previous models.” — OpenAI
OpenAI officially released GPT-5 yesterday, and the hype is real. Described as a “significant step along the path to AGI” by CEO Sam Altman, GPT-5 is touted as smarter, faster, and more accurate than its predecessors. It’s the first time a GPT model “felt like you can ask a legitimate expert, a PhD-level expert, anything,” according to Altman. In other words, using GPT-5 feels less like chatting with a bot and more like consulting an all-knowing expert on any topic. The model has a massively expanded context window (up to 256,000 tokens) for handling long conversations or documents, and OpenAI claims it hallucinates far less than GPT-4 – a big relief for users worried about AI “making stuff up.”
GPT-5’s new features have stunned observers. It excels at complex coding tasks, even capable of generating entire apps from a simple prompt. Altman quips that “software on demand is going to be one of the defining features of the GPT-5 era”, meaning you can ask GPT-5 to build programs or tools instantly. The model also shines in fields like finance, law, science, and medicine, making it a versatile assistant for professionals. Perhaps most importantly, GPT-5 is rolling out to all 700 million ChatGPT users – both free and paid – ensuring a huge global audience will immediately feel its impact. OpenAI even introduced lighter variants (like GPT-5-mini and GPT-5-nano) so everyone from casual users to enterprises can tap into its power. In Altman’s own lofty analogy, the leap from GPT-4 to GPT-5 is like going from a pixelated screen to a Retina display – a quantum jump in clarity and capability. It’s no surprise many are calling this the dawn of a new era in AI.
Claude 4.5: Anthropic’s Next Move
“Claude Opus 4 is the world’s best coding model.” — Anthropic
With GPT-5 raising the bar, rival Anthropic isn’t sitting still. Anthropic’s latest model, Claude 4 (notably the Claude Opus 4.1 update), recently “dominate[d] coding tests” by scoring 74.5% on a key software engineering benchmark – outperforming both OpenAI’s best GPT-4 model and Google’s Gemini 2.5. In fact, Claude 4.1 took the crown as the top coding assistant, cementing Anthropic’s reputation for AI programming prowess. This stronghold in coding capabilities puts pressure on GPT-5, which is now expected to match or exceed Claude on such tasks. Anthropic appears to be racing to keep its edge – some observers noted Claude 4.1 felt like a “rushed release to get ahead of GPT-5”. That hints Anthropic is determined not to be left behind.
So what’s next? Many speculate an even more advanced “Claude 4.5” (or similar) may be on the horizon as Anthropic’s answer to GPT-5. While details are under wraps, it’s a safe bet that the next Claude iteration will focus on closing any gaps GPT-5 opened. We can expect improvements in general reasoning and possibly a larger context window or enhanced tool use, building on features Claude 4 already introduced (like extended reasoning with web searches and coding assistance). Anthropic has publicly said Claude 4 is “the world’s best coding model”, and they’ll fight hard to maintain that title. If GPT-5 truly starts an AGI-like wave, Claude 4.5 could be Anthropic’s play to stay in the game, offering users an alternative AI assistant that’s just as intelligent – or even smarter in certain domains. It’s a classic AI arms race: GPT-5 raises the stakes, and Claude is gearing up to call.
Google’s Gemini 3: The Search Giant Strikes Back
“Gemini 3 references found in code hint at Google DeepMind’s next AI model.” — TestingCatalog
Not to be outdone, Google’s DeepMind team has been quietly preparing its counterpunch – rumored as Gemini 3.0. Code leaks and insider chatter suggest Google is working on Gemini 3 (with versions like “3.0 Flash” and “3.0 Pro”) as the next generation of their flagship AI. Why does this matter? Because Google’s Gemini 2.5 models are currently among the top AI models (Gemini 2.5 Pro was just slightly behind Claude on coding benchmarks). A jump to Gemini 3 could mark a major upgrade in capability. In fact, hints of a new “Deep Think” feature have been spotted – an advanced reasoning and chain-of-thought capability that Google reportedly has up its sleeve. This suggests Gemini 3 might excel at complex problem-solving and planning, potentially leveraging Google’s strength in multi-modal AI (combining text, images, maybe even video understanding in one model).
Importantly, the timing is telling. The Gemini 3 project was uncovered just as OpenAI’s GPT-5 and other rivals’ launches loomed. Many analysts think Google is positioning Gemini 3 as a direct answer to GPT-5, ensuring they don’t lose the AI crown. After all, Google kicked off the AI race years ago with its transformers and has vast resources – they likely won’t let GPT-5 dominate without a fight. We might see Gemini 3 debut with enhanced reasoning, better coding skills, and deep integration into Google’s ecosystem (imagine AI built into Search, Gmail, Android, etc.). For users, that means more choices: ChatGPT with GPT-5, Anthropic’s Claude, or Google’s Gemini – all competing to be the smartest AI assistant on the planet. This fierce competition could spur each to new heights, as each company tries to one-up the others in features and performance.
DeepSeek R2: The Uncommon Challenger from China
“The launch of DeepSeek’s R2 could be a pivotal moment in the AI industry.” — Reuters
Beyond the Silicon Valley heavyweights, a dark horse is emerging in the AI arena: DeepSeek R2. DeepSeek is a Chinese AI startup that stunned the tech world earlier this year with its R1 model, which reportedly rivaled Western models at a fraction of the cost. How extreme is it? R1 was so disruptive it “triggered a $1 trillion-plus sell-off in global equities” when it debuted, thanks to its cut-rate AI prowess. Now, DeepSeek is racing to launch R2, the successor, and experts say “the launch of DeepSeek’s R2 model could be a pivotal moment in the AI industry”. The reason: R2 is expected to be as powerful as the best models from OpenAI or Google, but dramatically cheaper and more efficient. Rumors suggest an ingenious design – a mixture-of-experts architecture with 1.2 trillion parameters (yes, trillion) where only 78 billion are active at once. In plain terms, R2 could match GPT-5’s skill while using far less computing power. One leak claims it may be ~97% cheaper to run than OpenAI’s top model, which, if true, would undercut the big players and democratize access to ultra-powerful AI.
DeepSeek R2 is also expected to be highly versatile: strong at coding, fluent in multiple languages (not just English), and even capable in vision and audio tasks. Chinese tech companies are already lining up to integrate DeepSeek’s models, and the U.S. government is reportedly worried, seeing R2 as a threat to U.S. AI leadership. However, R2’s release has been mired in drama – reports in June said DeepSeek’s CEO delayed the launch due to unsatisfactory performance, despite plans to release by May. There are also challenges like export restrictions on high-end chips for China, which could limit R2’s rollout. Still, whenever R2 does arrive, it could shock the industry by proving that innovation isn’t monopolized by the usual tech giants. Keep an eye on this one – it’s the uncommon contender that might change the AI game globally.
A New Era Begins – What’s Next?
GPT-5’s debut isn’t just another product launch; it feels like the opening chapter of a new era in AI. Suddenly, the frontier of what AI can do has jumped forward – and rivals are scrambling to catch up or leapfrog ahead. For consumers and businesses, this brewing AI arms race could mean rapid improvements in the tools we use every day. We’re talking smarter chatbots, AI assistants that can handle more complex tasks, and widespread AI integration from search engines to office software. OpenAI envisions GPT-5 ushering in an age of “AI experts at your fingertips,” and indeed, early demos show it coding entire programs and giving medical-style advice on command. Competitors like Anthropic and Google will push their models to do the same or better, while newcomers like DeepSeek promise to make high-end AI more accessible and affordable than ever. The pace of AI advancement is likely to accelerate as each player races not to be outdone.
For the tech industry, this new era could reshape the balance of power. If GPT-5 starts a revolution, we might see AI startups and incumbents alike investing even more heavily in research (the big tech firms are already spending hundreds of billions on AI data centers). We might also see AI models becoming competitive on quality and cost, not just one or the other – a win for users. Of course, it’s also a bit unpredictable: Will having AI this powerful at everyone’s fingertips change how we work or create content? Will it spark new innovations or new dilemmas (like how to ensure these models are used responsibly)? Those questions are just beginning. What’s clear is that GPT-5’s launch has lit a fire under the entire industry. A new chapter in the AI story is unfolding, and whether it’s GPT-5 leading the way or Claude, Gemini, DeepSeek and others catching up, one thing is certain – we are in for an exciting ride. The AI landscape a year from now could look utterly different. Buckle up, because the future that sci-fi promised might finally be arriving, one model at a time.
At a Glance: The New AI Titans (and How They Compare)
- OpenAI GPT-5: Just launched, general-purpose powerhouse. Excels in coding, writing, and complex reasoning with far fewer mistakes than prior models. Huge context window and new “thinking” mode make it feel almost like an AGI in training. Already available to 700M users via ChatGPT.
- Anthropic Claude 4/4.1 (toward “4.5”): Coding specialist and research-focused AI. Currently outperforms GPT-4 in programming tasks, and known for tool use and long-form reasoning. Likely to get even better soon to challenge GPT-5. Anthropic’s answer for those seeking an alternative AI with a safety-first approach.
- Google Gemini (v2.5 → v3.0): Google’s multimodal contender, designed to handle text, images, and more. Gemini 2.5 is strong (used in Google’s Bard and enterprise offerings), and Gemini 3 is anticipated to bring “deep thinking” abilities and tighter integration with Google’s products. Aims to match or beat GPT-5, backed by Google’s vast AI research.
- DeepSeek R2: The upstart from China, rumored to rival top Western models in intelligence while being dramatically cheaper to run. Focuses on reasoning, coding, and multilingual support. If it delivers on promises, it could open a new front in the AI race by breaking Big Tech’s monopoly. Release date is uncertain, but its impact could be global.
Each of these AI systems has its own strengths, but they’re all converging toward a common goal: more human-like intelligence accessible to everyone. The competition among them means the biggest winners may ultimately be us, the users, who will enjoy more powerful AI tools and faster innovation. The era of GPT-5 and its rivals is just beginning, and it promises to be one for the history books.
Sources: OpenAI/WIRED; Reuters; VentureBeat; TestingCatalog; Reuters; Overcast AI Hub.
Related Topics: #BREAKINGNEWS #MAG212 #MAG212NEWS #AI #GPT5 #GPT5PRO #OPENAI #SAMALTMAN #CLAUDE45 #ANTHROPIC #GEMINI3 #GOOGLEDEEPMIND #DEEPSEEKR2 #AIWARS #AGI #CODINGBENCHMARKS #SWEBENCH #REASONINGAI #MULTIMODAL #SAFETY #HALLUCINATIONS #ENTERPRISEAI #APIPRICING #CHATGPT #MICROSOFTAZURE #TECHINDUSTRY #INNOVATION #GLOBAL
International
New X Feature Reveals Where Users Really Are — And It’s Already Causing Chaos

November 25, 2025 – In a move to enhance transparency and curb the spread of bots and foreign influence on its platform, X (formerly Twitter) has launched a new “About This Account” feature that displays the country or region associated with user profiles. The tool, which rolled out widely in recent weeks, allows anyone to quickly check the origin of an account by tapping or hovering over the “Joined” date on a profile page. This comes amid growing concerns over online authenticity, especially in politically charged discussions.The feature pulls data from where the account was created or where it’s primarily active, providing a simple label like “United States” or “Europe.” X owner Elon Musk has touted it as a key step toward building trust, stating on the platform that it helps “expose fake accounts and foreign agitators.” Early adopters have praised it for its role in “instant bot detection,” with users reporting discoveries of profiles masquerading as locals but originating from distant regions.
Rollout and Initial Impact
The “About This Account” section was first tested on X employee profiles in October before a full launch in mid-November. However, the rollout wasn’t without hiccups—X briefly pulled the feature just hours after debut due to immediate backlash over privacy concerns, only to reinstate it shortly after. Since then, it has become a permanent fixture, also revealing additional details such as username change history and any connections to X’s premium services.The tool has already sparked heated debates. Proponents argue it reduces misinformation by highlighting potential foreign meddling; for instance, several accounts promoting political narratives, including pro-Palestinian voices and MAGA supporters, have been exposed as operating from countries like Pakistan, Bangladesh, Israel, or even Gaza—contradicting their portrayed identities. One viral thread highlighted “Gaza journalists” based overseas, fueling discussions about propaganda and influence operations.Critics, however, raise alarms about privacy and potential misuse. Some users worry it could lead to doxxing or harassment, especially for those in sensitive regions. Others note that savvy users might evade detection using VPNs, though X claims it’s refining its algorithms to improve accuracy. In response to feedback, the platform allows users to opt for a broader regional display (e.g., “Asia” instead of a specific country) to balance transparency with privacy.
Broader Implications for Social Media
This feature aligns with X’s ongoing efforts under Musk to prioritize free speech while tackling spam and inauthenticity. It arrives at a time when social platforms face scrutiny from regulators worldwide, including the EU’s Digital Services Act, which demands greater accountability for content moderation. Analysts suggest it could influence competitors like Meta’s Threads or Bluesky to adopt similar tools, potentially reshaping how users verify online identities.As global events like elections and conflicts amplify the role of social media, features like this could play a pivotal role in distinguishing genuine discourse from orchestrated campaigns. “It’s a double-edged sword,” says digital ethics expert Dr. Lena Vasquez in a recent interview. “While it promotes accountability, it also risks oversimplifying complex user behaviors in a borderless internet.”How to Use the “About This Account” FeatureAccessing and utilizing this tool is straightforward, making it accessible for everyday users to verify profiles. Here’s a step-by-step guide:
- View a Profile’s Location:
- Navigate to any user’s profile on X via the web, mobile app (iOS or Android), or desktop.
- Look for the “Joined [Date]” line below the user’s bio and profile picture.
- Tap (on mobile) or hover your cursor (on desktop) over the “Joined” date. A pop-up or expanded section titled “About This Account” will appear, showing the associated country or region.
- Check Additional Details:
- In the same pop-up, you’ll see username history (if changed) and any links to X services, like premium subscriptions.
- This is useful for spotting suspicious accounts—if a profile claims to be from one place but shows another, it might warrant further scrutiny.
- Customize Your Own Display (for Privacy):
- Go to your account settings on X.
- Under “Privacy and Safety,” find the “Account Information” or “Transparency” section (exact labeling may vary by update).
- Toggle the option to show a broader region instead of your specific country. Note: This doesn’t hide the data entirely but generalizes it (e.g., “North America” vs. “Canada”).
- Tips for Effective Use:
- Combine with other verification methods: Check for blue checkmarks (indicating verified status), post history, and engagement patterns.
- Report suspicious accounts via X’s built-in tools if you suspect bots or misinformation.
- Be mindful of privacy—avoid using this to harass others, as X’s policies prohibit doxxing.
While not foolproof, this feature empowers users to make more informed decisions about who they engage with online. As X continues to evolve, expect potential expansions, such as integrating AI-driven authenticity checks. For the latest updates, keep an eye on X’s official announcements or Musk’s posts.
business
Verizon Slashes Jobs in Record-Breaking Layoff — Here’s What We Know
Verizon announced a sweeping workforce reduction that will affect “more than” 13,000 employees — roughly 13% of its global headcount — in what CEO Dan Schulman calls the company’s largest-ever layoff. In an internal memo, Schulman says the move is intended to “simplify our operations to address the complexity and friction that slow us down and frustrate our customers.” The company also plans to cut outsourced and outside labor costs significantly. U.S.-based staff will begin receiving notifications today; employees outside the U.S. will be informed in the “coming weeks,” the Wall Street Journal reports
What Verizon says
- Reason: operational simplification and removing friction that hurts customer experience.
- Scale: “more than” 13,000 roles, about 13% of the workforce.
- Outsourcing: a significant reduction in outsourced and outside labor spending is part of the plan.
- Timing: U.S. notifications begin immediately; international notifications will follow.
Immediate impact
- Employees: tens of thousands will be affected directly or indirectly. U.S. notifications beginning today means many workers will learn their status immediately.
- Operations: Verizon says the goal is to reduce complexity and improve service — but short-term disruption to teams and projects is possible as roles are consolidated.
- Customers: Verizon frames the change as a way to speed decision-making and improve customer experience, though execution risk exists during the transition.
- Outsourced partners: vendors and contract workers can expect renegotiation or reductions.
What affected employees should do now
- Check official communications from HR and your manager for next steps and severance details.
- Ask about outplacement support (resume help, job counseling) and whether the company offers extended healthcare, COBRA assistance, or phased transitions.
- Document your work (accomplishments, repos, access) and secure personal copies of non-sensitive materials.
- File for unemployment as soon as possible where eligible and update LinkedIn and your network.
- Use company resources (employee assistance programs, career centers) and local talent services.
What managers and the company should prioritize
- Clear, compassionate communications and FAQs for affected employees.
- Fast, transparent explanation of severance, benefits continuation, and outplacement services.
- Careful workload redistribution and project continuity plans to avoid customer impact.
- A public-facing message to reassure customers and investors about service continuity and long-term strategy.
Market and strategic context (what this implies)
- Verizon is attempting aggressive cost reduction while refocusing on product and service quality (e.g., 5G, fixed wireless, enterprise services).
- Cutting outsourced labor and internal layers can reduce costs but carries execution risk: lost institutional knowledge, lowered morale, and short-term productivity dips.
- Investors may welcome lower operating expenses; customers and regulators will watch for service degradation.
data breaches
Cloudflare Outage Disrupts Global Internet — Company Restores Services After Major Traffic Spike

November 18, 2025 — MAG212NEWS
A significant outage at Cloudflare, one of the world’s leading internet infrastructure providers, caused widespread disruptions across major websites and online services on Tuesday. The incident, which began mid-morning GMT, temporarily affected access to platforms including ChatGPT, X (formerly Twitter), and numerous business, government, and educational services that rely on Cloudflare’s network.
According to Cloudflare, the outage was triggered by a sudden spike in “unusual traffic” flowing into one of its core services. The surge caused internal components to return 500-series error messages, leaving users unable to access services across regions in Europe, the Middle East, Asia, and North America.
Impact Across the Web
Because Cloudflare provides DNS, CDN, DDoS mitigation, and security services for millions of domains — powering an estimated 20% of global web traffic — the outage had swift and wide-reaching effects.
Users reported:
- Website loading failures
- “Internal Server Error” and “Bad Gateway” messages
- Slowdowns on major social platforms
- Inaccessibility of online tools, APIs, and third-party authentication services
The outage also briefly disrupted Cloudflare’s own customer-support portal, highlighting the interconnected nature of the company’s service ecosystem.
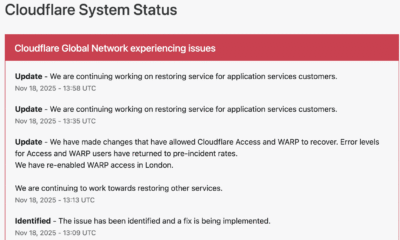
Cloudflare’s Response and Restoration
Cloudflare responded within minutes, publishing updates on its official status page and confirming that engineering teams were investigating the anomaly.
The company took the following steps to restore operations:
1. Rapid Detection and Acknowledgement
Cloudflare engineers identified elevated error rates tied to an internal service degradation. Public communications were issued to confirm the outage and reassure customers.
2. Isolating the Affected Systems
To contain the disruption, Cloudflare temporarily disabled or modified specific services in impacted regions. Notably, the company deactivated its WARP secure-connection service for users in London to stabilize network behavior while the fix was deployed.
3. Implementing Targeted Fixes
Technical teams rolled out configuration changes to Cloudflare Access and WARP, which successfully reduced error rates and restored normal traffic flow. Services were gradually re-enabled once systems were verified stable.
4. Ongoing Root-Cause Investigation
While the unusual-traffic spike remains the confirmed trigger, Cloudflare stated that a full internal analysis is underway to determine the exact source and prevent a recurrence.
By early afternoon UTC, Cloudflare confirmed that systems had returned to pre-incident performance levels, and affected services worldwide began functioning normally.
Why This Matters
Tuesday’s outage underscores a critical truth about modern internet architecture: a handful of infrastructure companies underpin a massive portion of global online activity. When one of them experiences instability — even briefly — the ripple effects are immediate and worldwide.
For businesses, schools, governments, and content creators, the incident is a reminder of the importance of:
- Redundant DNS/CDN providers
- Disaster-recovery and failover plans
- Clear communication protocols during service outages
- Vendor-dependency risk assessments
Cloudflare emphasized that no evidence currently points to a cyberattack, though the nature of the traffic spike remains under investigation.
Looking Ahead
As Cloudflare completes its post-incident review, the company is expected to provide a detailed breakdown of the technical root cause and outline steps to harden its infrastructure. Given Cloudflare’s central role in global internet stability, analysts say the findings will be watched closely by governments, cybersecurity professionals, and enterprise clients.
For now, services are restored — but the outage serves as a powerful reminder of how interconnected and vulnerable the global web can be.