International
The Truth About Hakimi’s Ballon d’Or Snub—And Why It Matters
In a season defined by excellence and understated brilliance, Moroccan star Achraf Hakimi has elevated his status to one of football’s most complete and influential players. Whether orchestrating attacks from deep, delivering match-winning assists, or locking down world-class attackers, Hakimi’s 2024–2025 campaign has been a masterclass in tactical intelligence, physical dynamism, and leadership.
Yet despite his critical contributions across club and international football, Hakimi’s name remains largely absent from the Ballon d’Or conversation—underscoring longstanding biases in how global football rewards excellence.
“He doesn’t just play his position—he changes the way the entire team operates.”
— Luis Enrique, Former PSG Coach
A Season of Achievements That Define Greatness
Hakimi’s season was nothing short of historic, marked by elite performances and record-breaking accolades:
- 🏆 Champions League winner with PSG
- 🇫🇷 Ligue 1 & Coupe de France titles
- ⚽ 9 goals & 14 assists as a right-back
- 🔥 Scored in the UEFA Champions League final
- 🌍 World Cup semifinalist with Morocco
- 🥉 Olympic bronze medalist
- 👑 Best African Player in Ligue 1
He contributed to 20+ goals across all competitions for Paris Saint-Germain—not just through assists and goals, but through pressing, ball recovery, and match control. His partnership with Kylian Mbappé and Ousmane Dembélé turned PSG’s right flank into a relentless attacking force feared across Europe.
In the Champions League, Hakimi delivered standout performances against top-tier opposition including Bayern Munich and Manchester City, combining his signature overlapping runs with rock-solid defensive displays. In the final, he scored a pivotal goal—cementing his influence in the club’s first-ever Champions League triumph.
Elevating Others: The Hidden Value of Hakimi
Hakimi’s greatness is most evident in how he amplifies those around him.
- He revitalized Romelu Lukaku’s form at Inter Milan.
- He offered consistent tactical support to Hakim Ziyech with the Moroccan national team.
- He helped Dembélé rediscover his rhythm at PSG after years of inconsistency at Barcelona.
“He brings freedom to attackers because they know he’ll always be there behind them.”
— Thierry Marchal, Football Analyst
The Case for the Ballon d’Or
Football awards often prioritize highlight reels and goal counts—but Hakimi’s game has always been about substance over flash.
- Consistency: Week after week, Hakimi delivered at the highest level in France, Europe, and Africa.
- Impact: He dictates tempo from defense, covers vast ground, and initiates attacks with vision and precision.
- Leadership: As a senior figure for Morocco, he has become a symbol of African football’s global ascent.
“People always talk about strikers for the Ballon d’Or, but if you’ve watched this season closely, Hakimi has been on another level. He deserves to be on that podium—no question.”
— Kylian Mbappé, PSG & France forward
Why He Might Be Overlooked
Despite his undeniable influence, systemic factors may keep Hakimi from lifting the Ballon d’Or:
- Positional Bias
Defenders—and especially full-backs—are rarely honored. The last defender to win the Ballon d’Or was Fabio Cannavaro in 2006. No full-back has ever claimed the award. - Media Spotlight
Voting tends to favor forwards like Mbappé, Haaland, or Vinícius Jr., whose goal stats and highlight reels dominate headlines. - Continental Bias
African players, regardless of performance, often face diminished recognition. Legends like Samuel Eto’o and Didier Drogba were frequently overlooked despite exceptional seasons. - Team Spotlight
Although PSG claimed the treble, the club’s recent history and media narratives may have diverted attention from Hakimi’s central role.
Conclusion: A Modern Legend, Deserving of More
Achraf Hakimi’s 2024–2025 season was more than just successful—it was transformative. He broke positional stereotypes, led by example, and delivered when it mattered most. His candidacy for the Ballon d’Or represents more than a personal milestone; it challenges football to broaden its definition of greatness.
“Until the system rewards balance over branding, players like Hakimi will always be overlooked.”
— Diego Fernandez, Football Ethics Scholar
Whether or not he lifts the trophy, one thing is certain: Hakimi belongs in the Ballon d’Or conversation—and perhaps, in a more inclusive future, in the winner’s circle.
International
New X Feature Reveals Where Users Really Are — And It’s Already Causing Chaos

November 25, 2025 – In a move to enhance transparency and curb the spread of bots and foreign influence on its platform, X (formerly Twitter) has launched a new “About This Account” feature that displays the country or region associated with user profiles. The tool, which rolled out widely in recent weeks, allows anyone to quickly check the origin of an account by tapping or hovering over the “Joined” date on a profile page. This comes amid growing concerns over online authenticity, especially in politically charged discussions.The feature pulls data from where the account was created or where it’s primarily active, providing a simple label like “United States” or “Europe.” X owner Elon Musk has touted it as a key step toward building trust, stating on the platform that it helps “expose fake accounts and foreign agitators.” Early adopters have praised it for its role in “instant bot detection,” with users reporting discoveries of profiles masquerading as locals but originating from distant regions.
Rollout and Initial Impact
The “About This Account” section was first tested on X employee profiles in October before a full launch in mid-November. However, the rollout wasn’t without hiccups—X briefly pulled the feature just hours after debut due to immediate backlash over privacy concerns, only to reinstate it shortly after. Since then, it has become a permanent fixture, also revealing additional details such as username change history and any connections to X’s premium services.The tool has already sparked heated debates. Proponents argue it reduces misinformation by highlighting potential foreign meddling; for instance, several accounts promoting political narratives, including pro-Palestinian voices and MAGA supporters, have been exposed as operating from countries like Pakistan, Bangladesh, Israel, or even Gaza—contradicting their portrayed identities. One viral thread highlighted “Gaza journalists” based overseas, fueling discussions about propaganda and influence operations.Critics, however, raise alarms about privacy and potential misuse. Some users worry it could lead to doxxing or harassment, especially for those in sensitive regions. Others note that savvy users might evade detection using VPNs, though X claims it’s refining its algorithms to improve accuracy. In response to feedback, the platform allows users to opt for a broader regional display (e.g., “Asia” instead of a specific country) to balance transparency with privacy.
Broader Implications for Social Media
This feature aligns with X’s ongoing efforts under Musk to prioritize free speech while tackling spam and inauthenticity. It arrives at a time when social platforms face scrutiny from regulators worldwide, including the EU’s Digital Services Act, which demands greater accountability for content moderation. Analysts suggest it could influence competitors like Meta’s Threads or Bluesky to adopt similar tools, potentially reshaping how users verify online identities.As global events like elections and conflicts amplify the role of social media, features like this could play a pivotal role in distinguishing genuine discourse from orchestrated campaigns. “It’s a double-edged sword,” says digital ethics expert Dr. Lena Vasquez in a recent interview. “While it promotes accountability, it also risks oversimplifying complex user behaviors in a borderless internet.”How to Use the “About This Account” FeatureAccessing and utilizing this tool is straightforward, making it accessible for everyday users to verify profiles. Here’s a step-by-step guide:
- View a Profile’s Location:
- Navigate to any user’s profile on X via the web, mobile app (iOS or Android), or desktop.
- Look for the “Joined [Date]” line below the user’s bio and profile picture.
- Tap (on mobile) or hover your cursor (on desktop) over the “Joined” date. A pop-up or expanded section titled “About This Account” will appear, showing the associated country or region.
- Check Additional Details:
- In the same pop-up, you’ll see username history (if changed) and any links to X services, like premium subscriptions.
- This is useful for spotting suspicious accounts—if a profile claims to be from one place but shows another, it might warrant further scrutiny.
- Customize Your Own Display (for Privacy):
- Go to your account settings on X.
- Under “Privacy and Safety,” find the “Account Information” or “Transparency” section (exact labeling may vary by update).
- Toggle the option to show a broader region instead of your specific country. Note: This doesn’t hide the data entirely but generalizes it (e.g., “North America” vs. “Canada”).
- Tips for Effective Use:
- Combine with other verification methods: Check for blue checkmarks (indicating verified status), post history, and engagement patterns.
- Report suspicious accounts via X’s built-in tools if you suspect bots or misinformation.
- Be mindful of privacy—avoid using this to harass others, as X’s policies prohibit doxxing.
While not foolproof, this feature empowers users to make more informed decisions about who they engage with online. As X continues to evolve, expect potential expansions, such as integrating AI-driven authenticity checks. For the latest updates, keep an eye on X’s official announcements or Musk’s posts.
business
Verizon Slashes Jobs in Record-Breaking Layoff — Here’s What We Know
Verizon announced a sweeping workforce reduction that will affect “more than” 13,000 employees — roughly 13% of its global headcount — in what CEO Dan Schulman calls the company’s largest-ever layoff. In an internal memo, Schulman says the move is intended to “simplify our operations to address the complexity and friction that slow us down and frustrate our customers.” The company also plans to cut outsourced and outside labor costs significantly. U.S.-based staff will begin receiving notifications today; employees outside the U.S. will be informed in the “coming weeks,” the Wall Street Journal reports
What Verizon says
- Reason: operational simplification and removing friction that hurts customer experience.
- Scale: “more than” 13,000 roles, about 13% of the workforce.
- Outsourcing: a significant reduction in outsourced and outside labor spending is part of the plan.
- Timing: U.S. notifications begin immediately; international notifications will follow.
Immediate impact
- Employees: tens of thousands will be affected directly or indirectly. U.S. notifications beginning today means many workers will learn their status immediately.
- Operations: Verizon says the goal is to reduce complexity and improve service — but short-term disruption to teams and projects is possible as roles are consolidated.
- Customers: Verizon frames the change as a way to speed decision-making and improve customer experience, though execution risk exists during the transition.
- Outsourced partners: vendors and contract workers can expect renegotiation or reductions.
What affected employees should do now
- Check official communications from HR and your manager for next steps and severance details.
- Ask about outplacement support (resume help, job counseling) and whether the company offers extended healthcare, COBRA assistance, or phased transitions.
- Document your work (accomplishments, repos, access) and secure personal copies of non-sensitive materials.
- File for unemployment as soon as possible where eligible and update LinkedIn and your network.
- Use company resources (employee assistance programs, career centers) and local talent services.
What managers and the company should prioritize
- Clear, compassionate communications and FAQs for affected employees.
- Fast, transparent explanation of severance, benefits continuation, and outplacement services.
- Careful workload redistribution and project continuity plans to avoid customer impact.
- A public-facing message to reassure customers and investors about service continuity and long-term strategy.
Market and strategic context (what this implies)
- Verizon is attempting aggressive cost reduction while refocusing on product and service quality (e.g., 5G, fixed wireless, enterprise services).
- Cutting outsourced labor and internal layers can reduce costs but carries execution risk: lost institutional knowledge, lowered morale, and short-term productivity dips.
- Investors may welcome lower operating expenses; customers and regulators will watch for service degradation.
data breaches
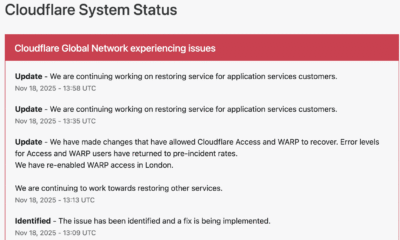
Cloudflare Outage Disrupts Global Internet — Company Restores Services After Major Traffic Spike

November 18, 2025 — MAG212NEWS
A significant outage at Cloudflare, one of the world’s leading internet infrastructure providers, caused widespread disruptions across major websites and online services on Tuesday. The incident, which began mid-morning GMT, temporarily affected access to platforms including ChatGPT, X (formerly Twitter), and numerous business, government, and educational services that rely on Cloudflare’s network.
According to Cloudflare, the outage was triggered by a sudden spike in “unusual traffic” flowing into one of its core services. The surge caused internal components to return 500-series error messages, leaving users unable to access services across regions in Europe, the Middle East, Asia, and North America.
Impact Across the Web
Because Cloudflare provides DNS, CDN, DDoS mitigation, and security services for millions of domains — powering an estimated 20% of global web traffic — the outage had swift and wide-reaching effects.
Users reported:
- Website loading failures
- “Internal Server Error” and “Bad Gateway” messages
- Slowdowns on major social platforms
- Inaccessibility of online tools, APIs, and third-party authentication services
The outage also briefly disrupted Cloudflare’s own customer-support portal, highlighting the interconnected nature of the company’s service ecosystem.
Cloudflare’s Response and Restoration
Cloudflare responded within minutes, publishing updates on its official status page and confirming that engineering teams were investigating the anomaly.
The company took the following steps to restore operations:
1. Rapid Detection and Acknowledgement
Cloudflare engineers identified elevated error rates tied to an internal service degradation. Public communications were issued to confirm the outage and reassure customers.
2. Isolating the Affected Systems
To contain the disruption, Cloudflare temporarily disabled or modified specific services in impacted regions. Notably, the company deactivated its WARP secure-connection service for users in London to stabilize network behavior while the fix was deployed.
3. Implementing Targeted Fixes
Technical teams rolled out configuration changes to Cloudflare Access and WARP, which successfully reduced error rates and restored normal traffic flow. Services were gradually re-enabled once systems were verified stable.
4. Ongoing Root-Cause Investigation
While the unusual-traffic spike remains the confirmed trigger, Cloudflare stated that a full internal analysis is underway to determine the exact source and prevent a recurrence.
By early afternoon UTC, Cloudflare confirmed that systems had returned to pre-incident performance levels, and affected services worldwide began functioning normally.
Why This Matters
Tuesday’s outage underscores a critical truth about modern internet architecture: a handful of infrastructure companies underpin a massive portion of global online activity. When one of them experiences instability — even briefly — the ripple effects are immediate and worldwide.
For businesses, schools, governments, and content creators, the incident is a reminder of the importance of:
- Redundant DNS/CDN providers
- Disaster-recovery and failover plans
- Clear communication protocols during service outages
- Vendor-dependency risk assessments
Cloudflare emphasized that no evidence currently points to a cyberattack, though the nature of the traffic spike remains under investigation.
Looking Ahead
As Cloudflare completes its post-incident review, the company is expected to provide a detailed breakdown of the technical root cause and outline steps to harden its infrastructure. Given Cloudflare’s central role in global internet stability, analysts say the findings will be watched closely by governments, cybersecurity professionals, and enterprise clients.
For now, services are restored — but the outage serves as a powerful reminder of how interconnected and vulnerable the global web can be.