


Two-day February intrusion leaked financial and medical details; group begins notifications and offers credit monitoring as regulators are alerted. The Business Council of New York State...



Leaked SIM and PUK data heighten SIM-swapping risks as critics fault Orange’s response; company says no passwords, emails or banking data were taken. Orange Belgium disclosed...



Attackers use CVE-2023-46604 to breach Linux cloud hosts, drop “DripDropper” malware, and quietly fix the flaw to lock in access, researchers say. Threat actors are abusing...



Contact data for ~280k email accounts and 1.7k modem passwords accessed; breach isolated to iiNet order system, company says Australia’s TPG Telecom disclosed unauthorized access to...



Colt Technology Services’ internal systems remain down after a suspected ransomware attack; WarLock gang claims to have stolen 1 million documents, demanding $200K ransom Colt Technology...
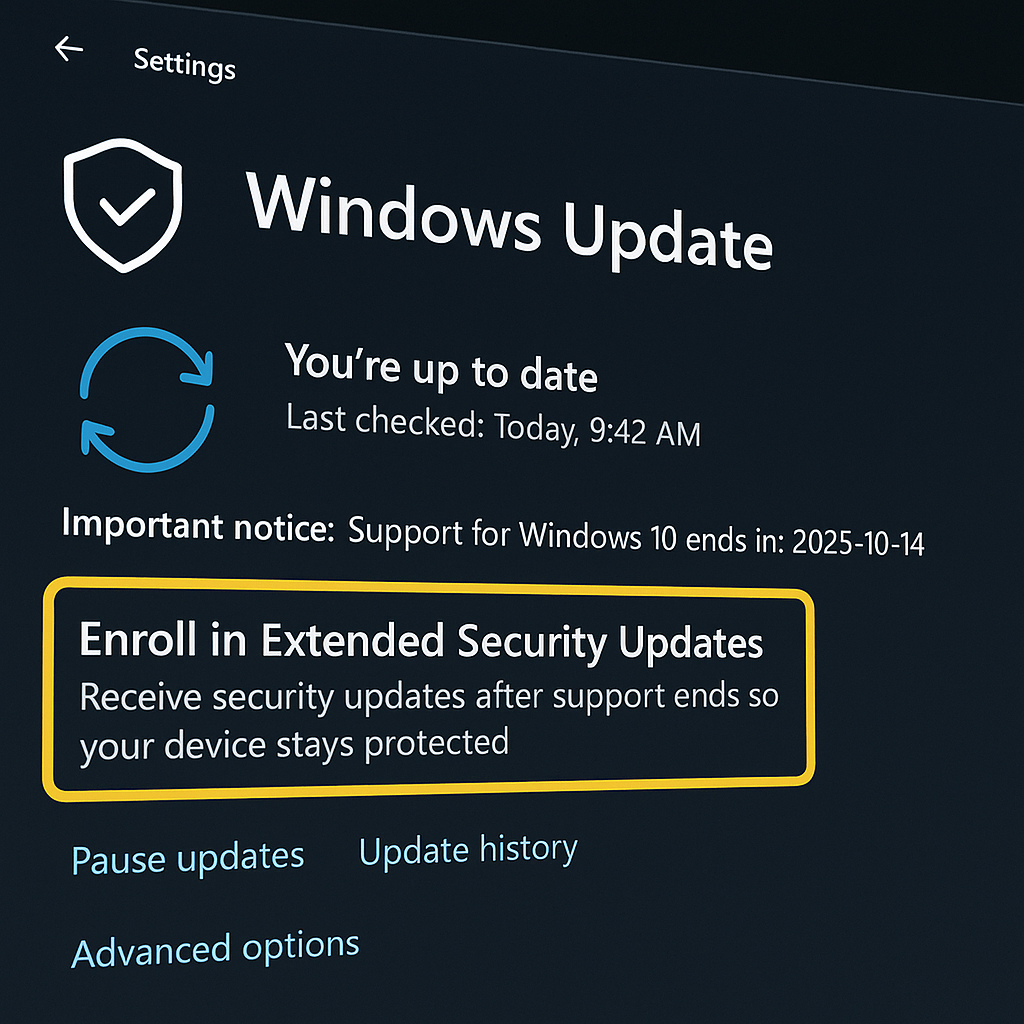
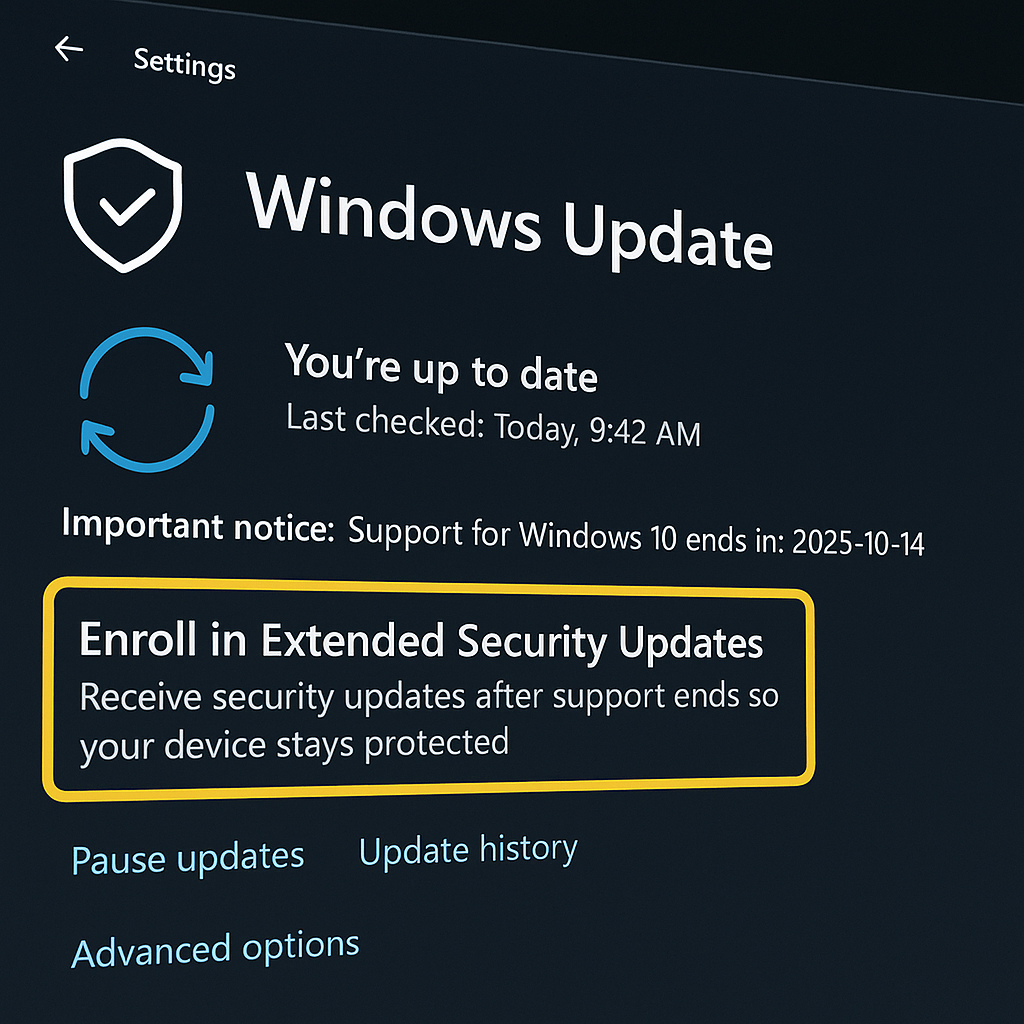
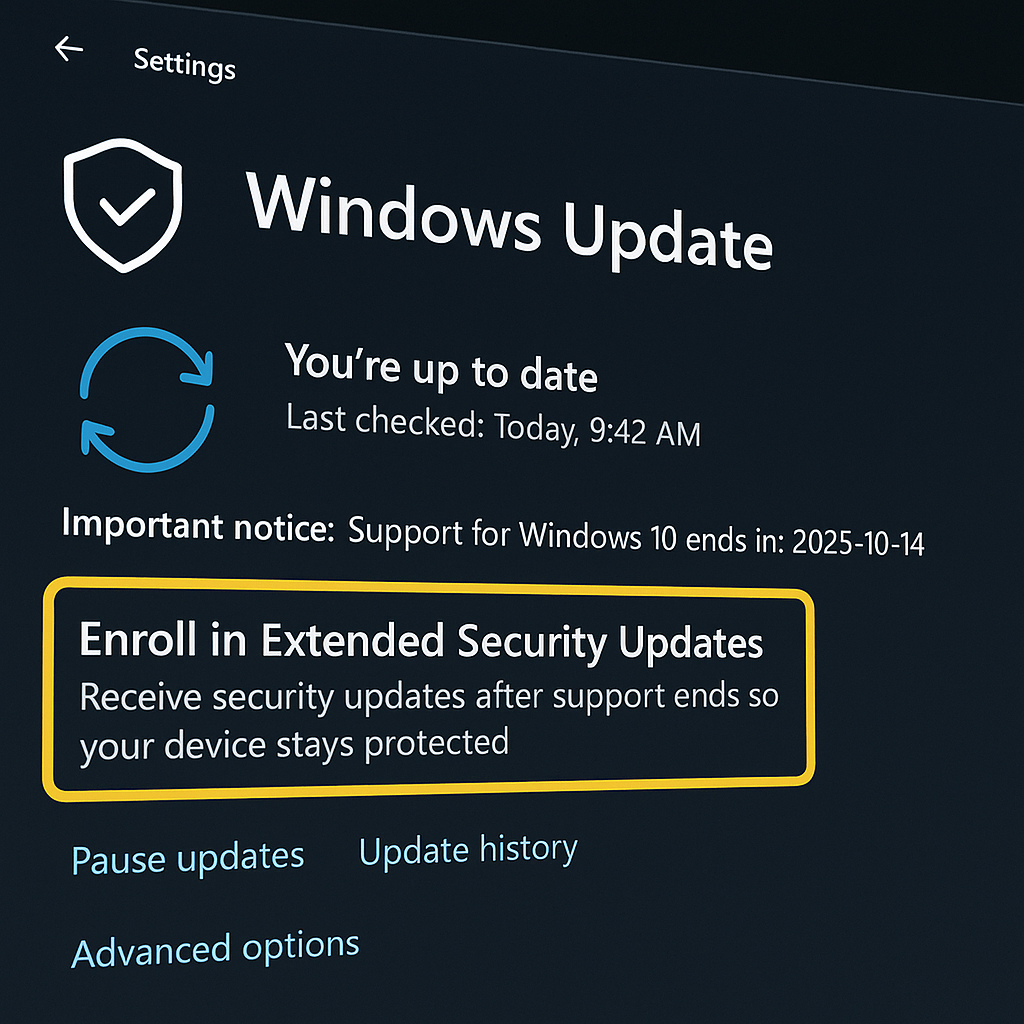
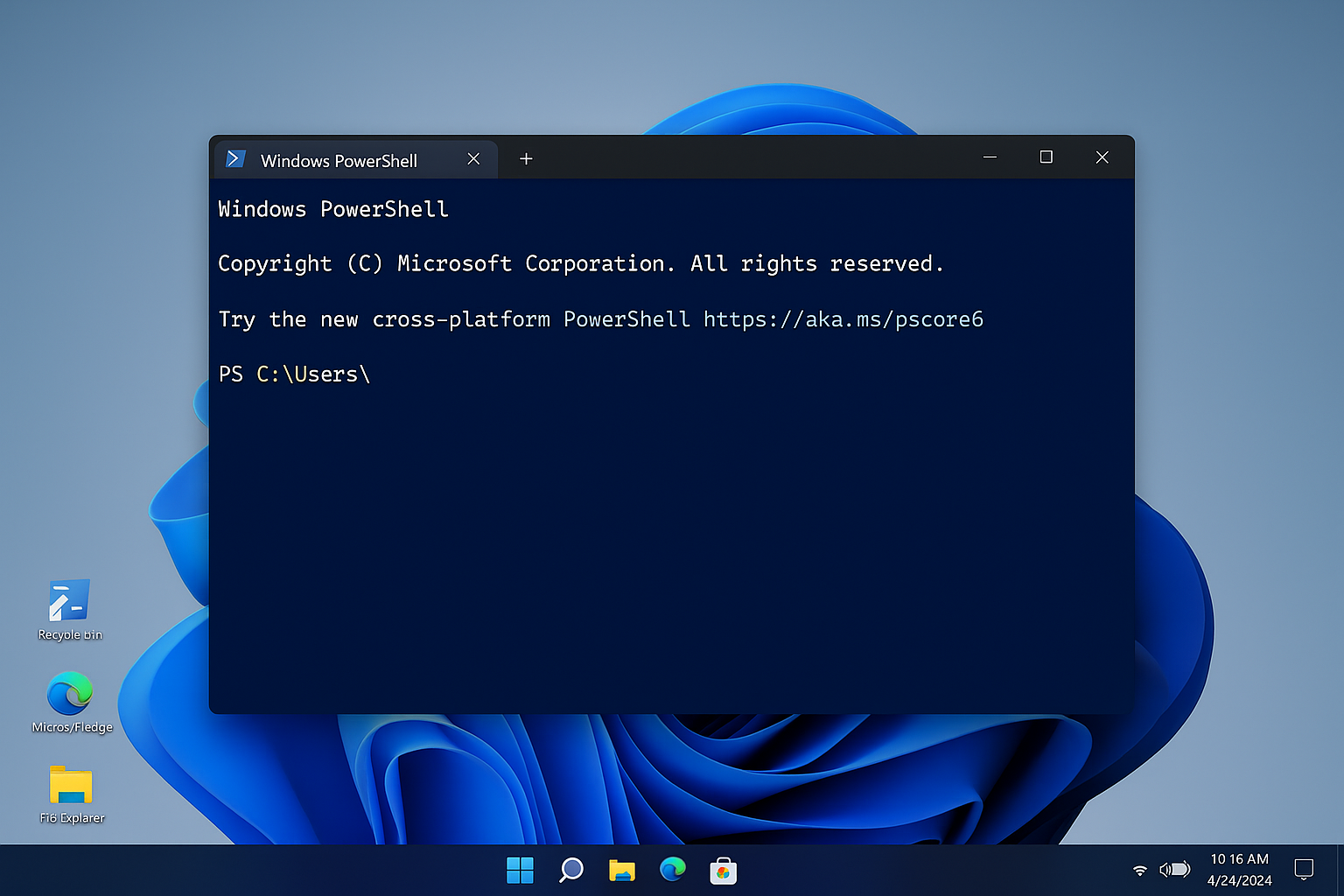
Free support ends October 14, 2025; new KB5063709 unlocks Extended Security Updates enrollment to keep critical patches flowing through October 2026. Microsoft is warning Windows 10...



Russian-linked group EncryptHub is impersonating IT staff on Microsoft Teams, walking victims into remote sessions, then abusing CVE-2025-26633 (“MSC EvilTwin”) to execute rogue .msc consoles and...


What Pegasus actually does Pegasus is a commercial “mercenary” spyware suite by NSO Group that covertly compromises iOS and Android devices, enabling data theft (messages, photos,...
From August–September 2025, Windows 11 24H2 and Windows Server 2025 drop the legacy engine to simplify the OS and close a long-abused security gap. Microsoft will...



From permits to youth benefits, the kingdom consolidates e-government portals for residents and the diaspora. RABAT, Morocco — Morocco’s government is expanding a network of official...