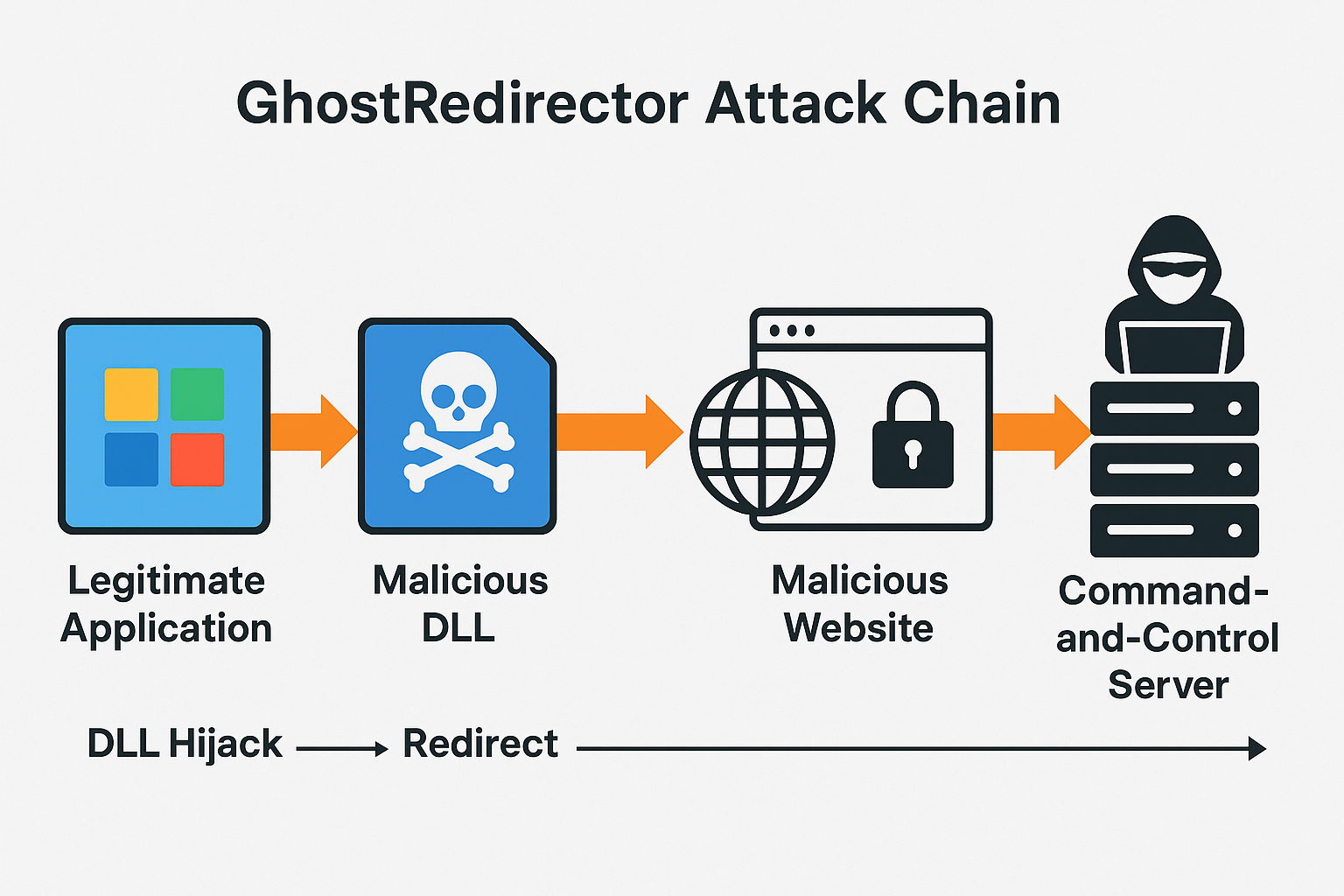
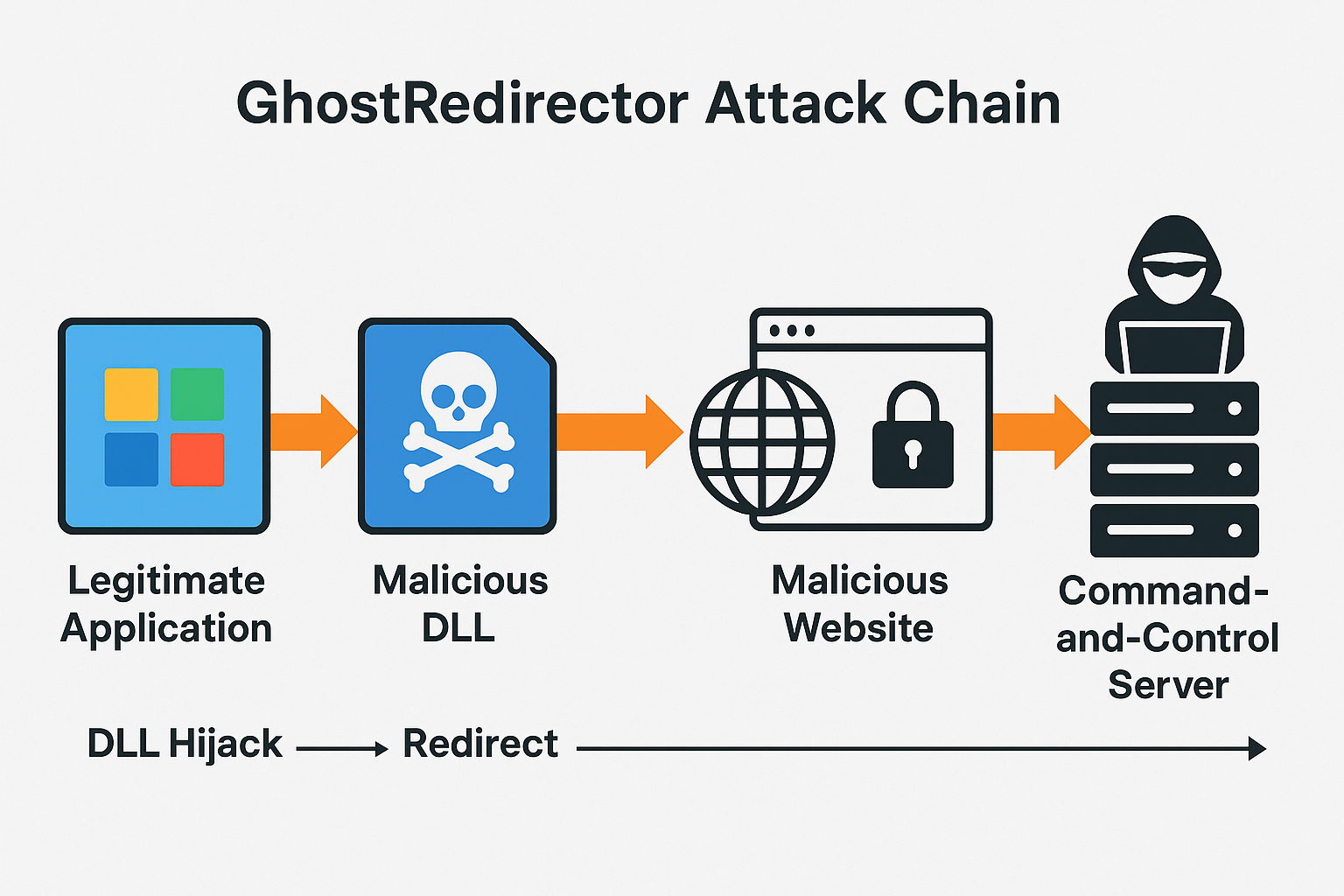
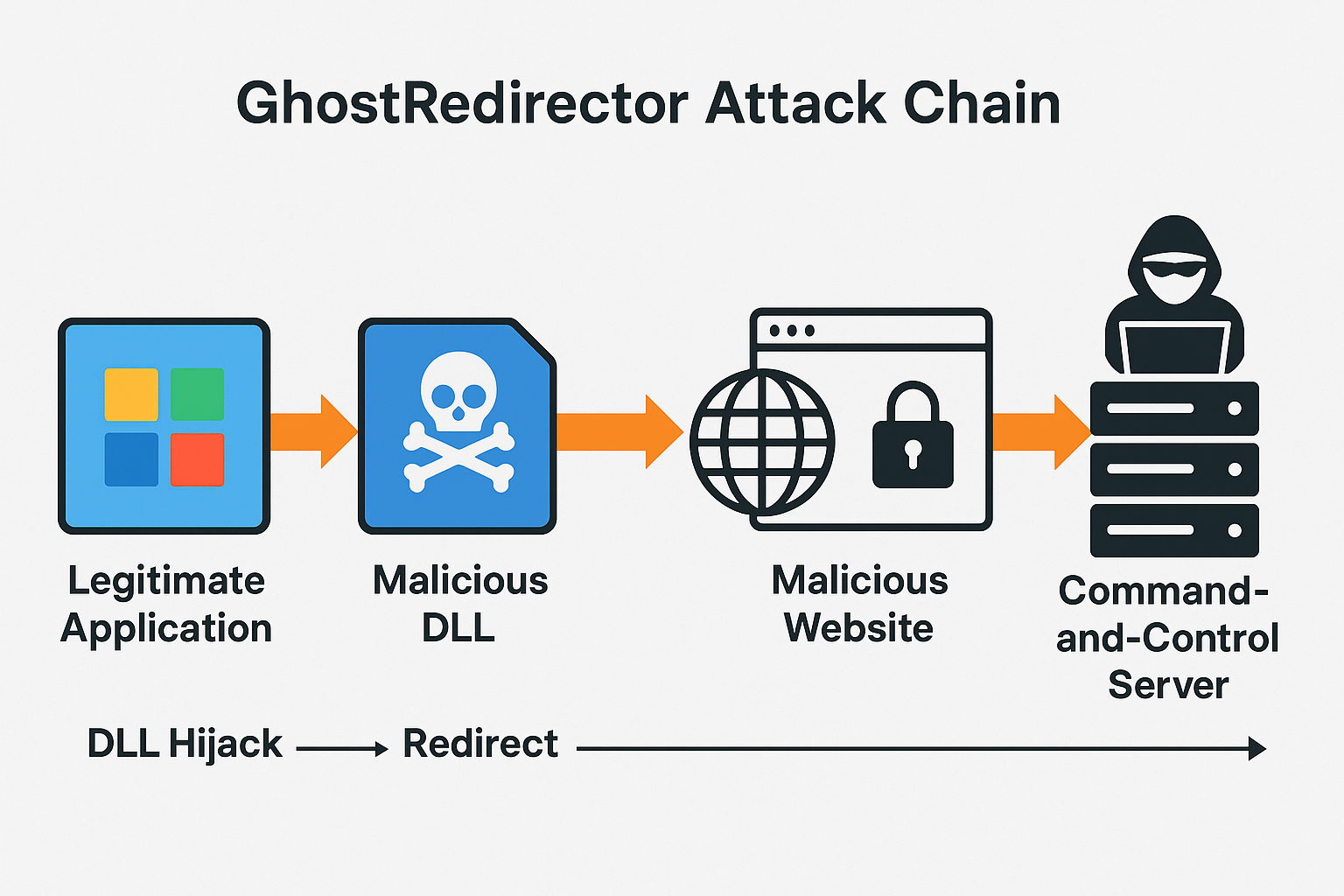
Cybercriminals abuse trusted Windows executables to redirect users, spread malware, and harvest sensitive data. A new malware campaign dubbed GhostRedirector has compromised more than 65 legitimate...



Threat actors abuse misconfigurations and living-off-the-land tools—using fake 404 pages and panda JPEG “polyglot” files—to drop miners on Linux and Windows at scale. Twin campaigns dubbed...



Russian-linked group EncryptHub is impersonating IT staff on Microsoft Teams, walking victims into remote sessions, then abusing CVE-2025-26633 (“MSC EvilTwin”) to execute rogue .msc consoles and...
From August–September 2025, Windows 11 24H2 and Windows Server 2025 drop the legacy engine to simplify the OS and close a long-abused security gap. Microsoft will...
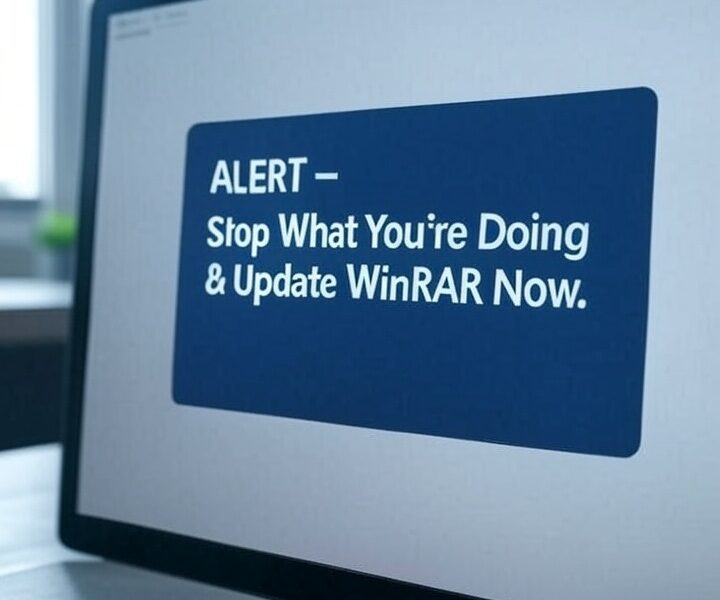

A zero-day flaw (CVE-2025-8088) is under active attack by Russian-linked groups Paper Werewolf and RomCom. Booby-trapped archives can plant malware in Windows startup folders—silently hijacking your...
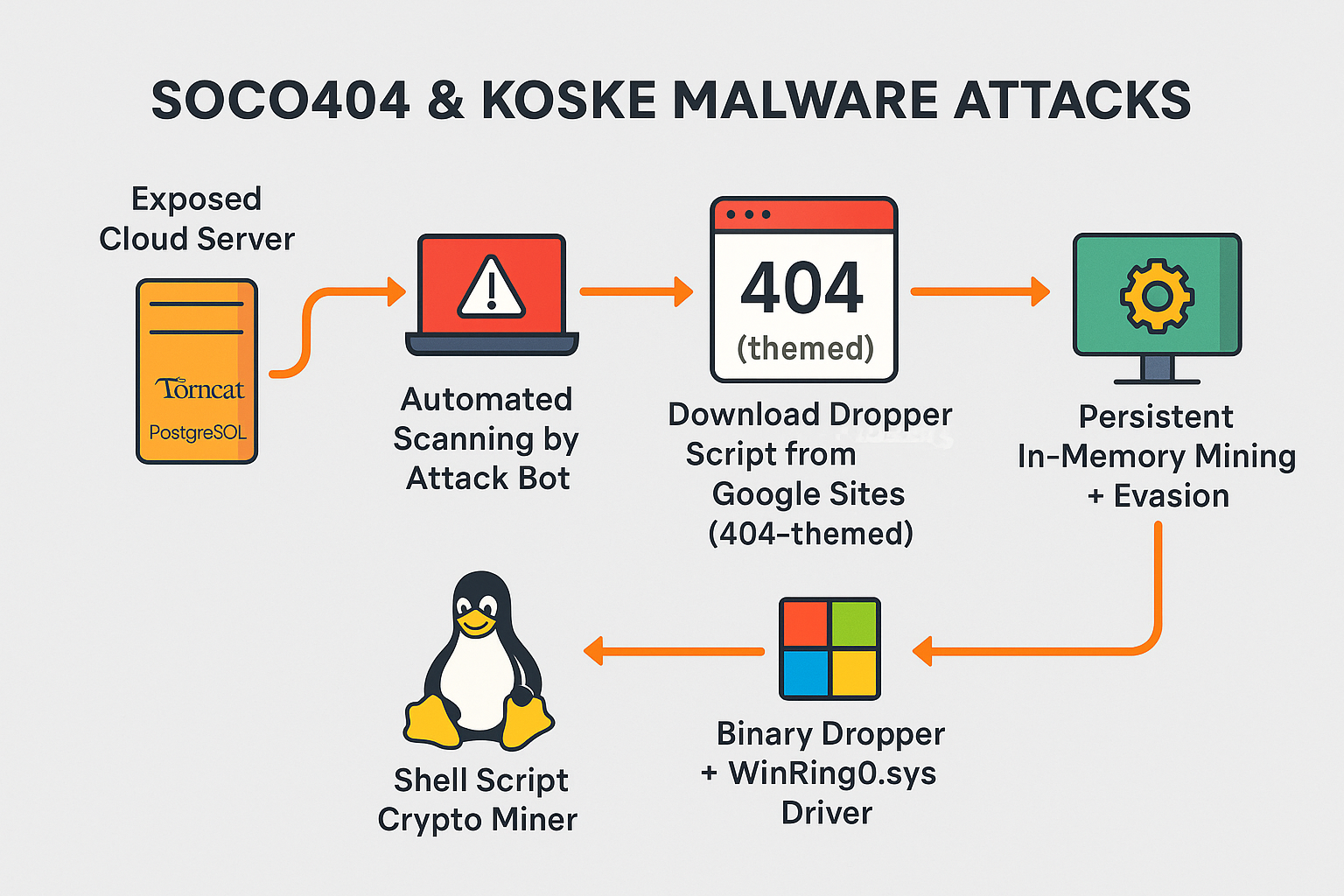
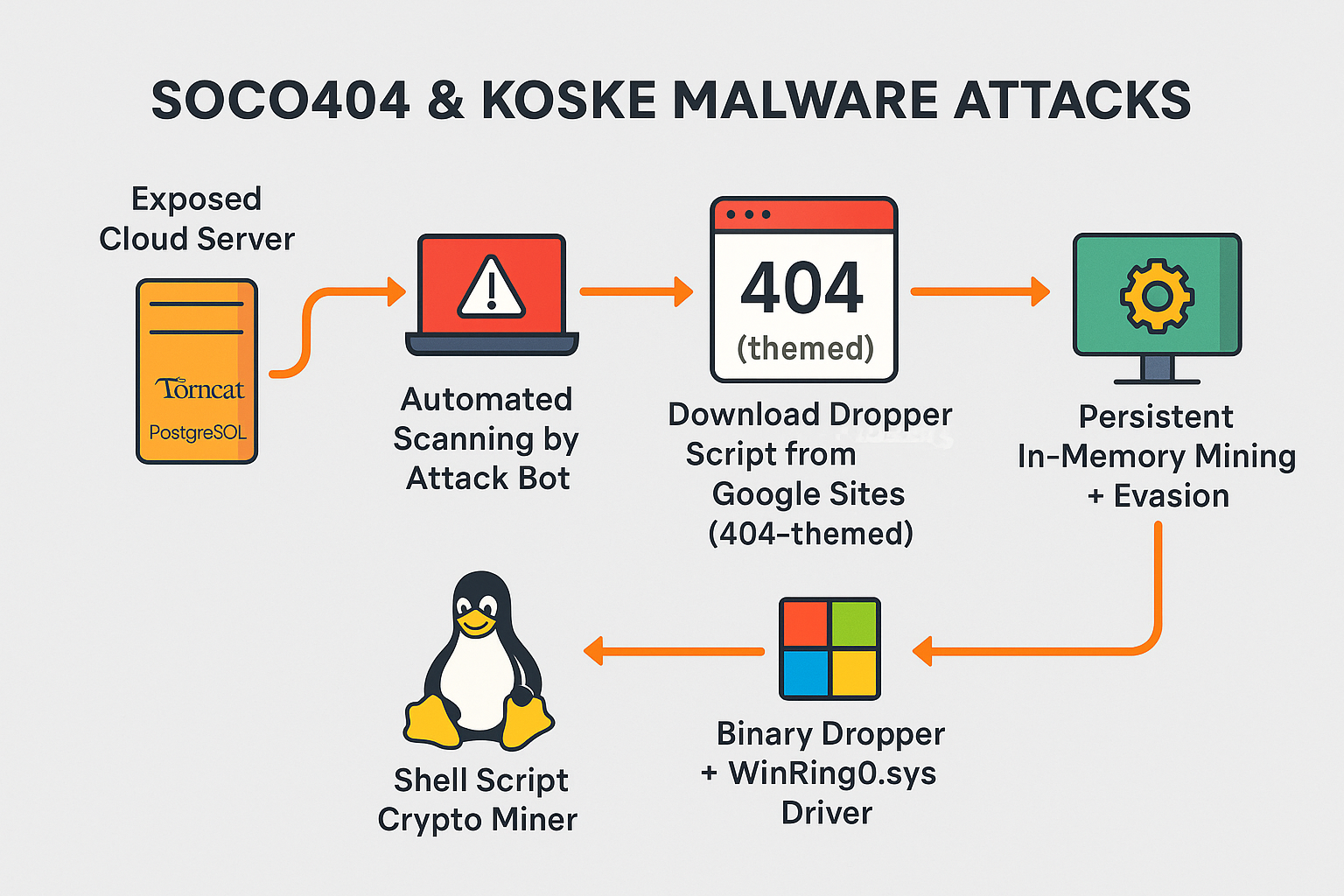
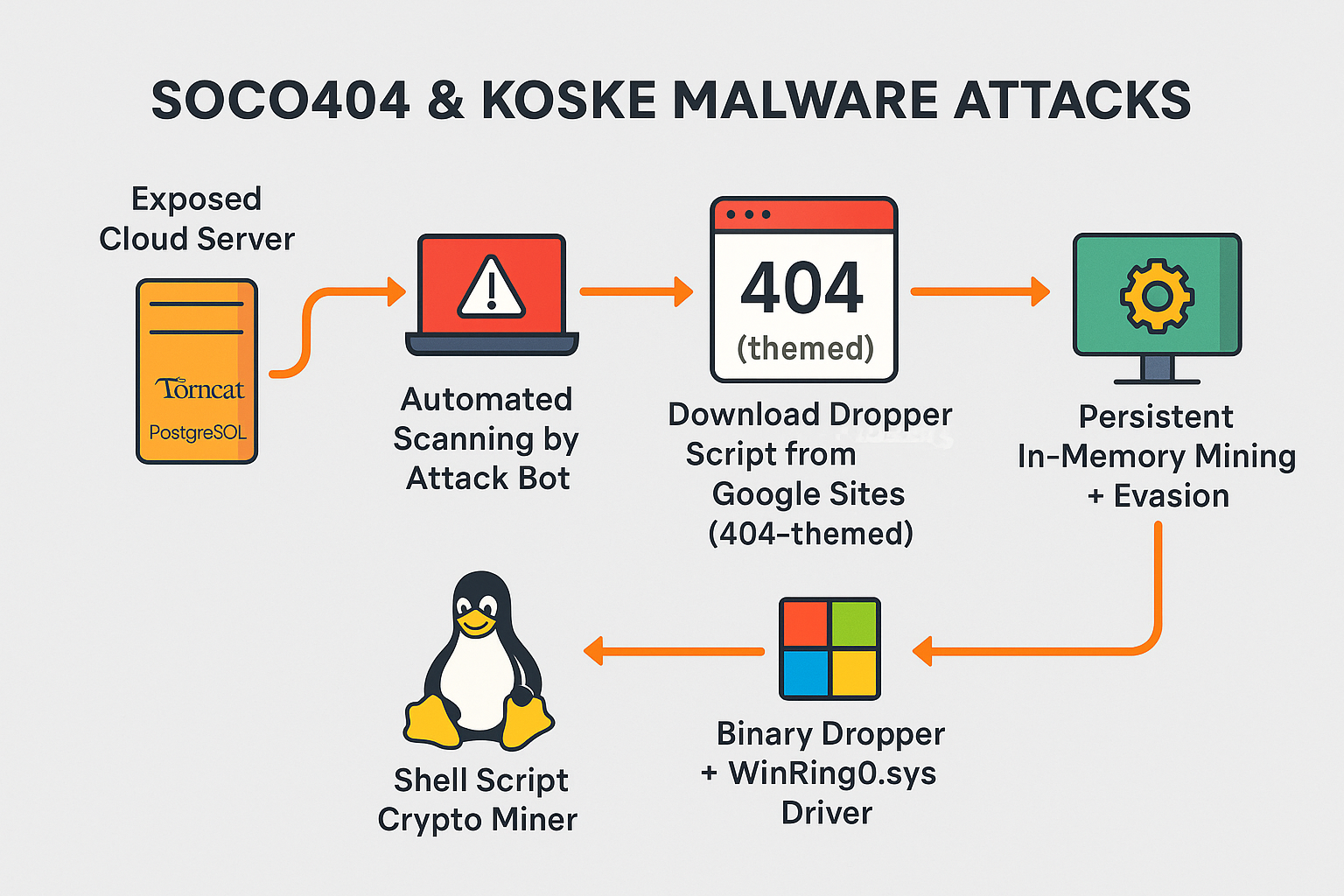
New cross-platform malware strains abuse PostgreSQL, Tomcat, JupyterLab, and Confluence to hijack compute power for cryptocurrency mining—leaving cloud workloads vulnerable and detection difficult. 🧨 Introduction: Clouds...